
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. Platforms like SAGA by Munit.io deliver these insights in real time, so security teams can move from reactive to proactive defense. By identifying early-stage threat coordination or mentions of internal assets, organizations can take preventative action before attacks escalate. Likewise, this proactive approach helps strengthen overall cyber resilience. While the Deep Web supports secure infrastructure, the Dark Web demands stricter monitoring because of its potential for criminal use.
Evading government restrictions to explore new political ideologies can be an imprisonable offense in some countries. China uses what is known as the “Great Firewall” limit access to popular sites for this exact reason. The risk of being a visitor to this content could lead to being placed on a watchlist or immediate targeting for a jail sentence.
The Hidden Wiki

This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. For this reason, you must watch out and avoid opening anything that looks suspicious to you. You should never use your personal information on the dark web anywhere else in your life. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web.
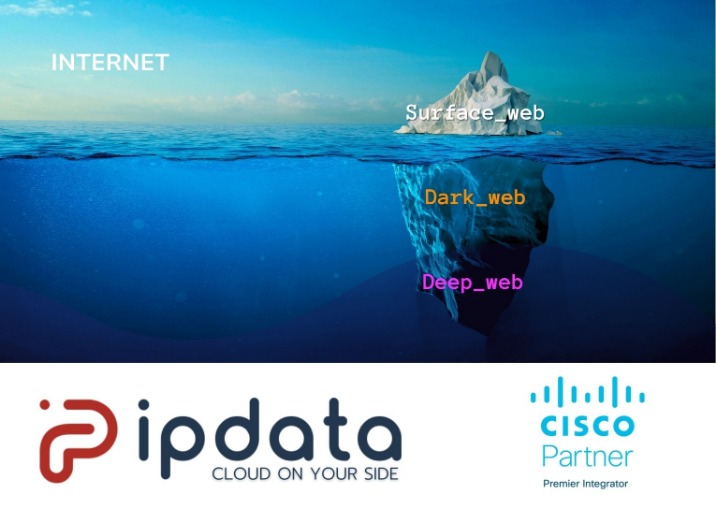
Legitimate uses of the Deep Web include accessing medical records, conducting financial transactions, researching academic databases, and managing secure corporate intranets. Organizations must monitor the Deep Web for potential data breaches or unauthorized access to proprietary information. Cybersecurity tools and techniques, such as Deep Web monitoring, help mitigate these risks. The anonymity offered by the Deep Web can be exploited for illicit purposes, such as selling illegal drugs, weapons, or stolen data. This is especially true for the Dark Web, where platforms like Silk Road (a now-defunct marketplace) once operated. The Deep Web serves legitimate purposes, while the Dark Web, a smaller subset of the Deep Web, is known for hosting illegal activities, black markets, and controversial forums.
PrivateAlps
Additionally, ensure you do not visit websites or social media that might require you to drop your personal details. To discover content on the web, search engines use web crawlers that follow hyperlinks through known protocol virtual port numbers. This technique is ideal for discovering content on the surface web but is often ineffective at finding deep web content. Ultimately, the responsibility lies with individuals to govern their online conduct wisely. Prioritizing internet safety—utilizing encryption, employing secure passwords, practicing cautious engagement—can significantly reduce experiences of danger in both the deep and dark webs. As digital landscapes continue to evolve, so too must our commitment to understanding and navigating these complexities safely.
Accessing Onion Sites On Android
Users can access pages on the deep web via a direct URL or IP address, but they will need to pass through further security measures before they can access the content. Finally, law enforcement agencies can access the dark web to detect illegal activity, such as weapon deals, drug distribution, and financial crimes. For instance, money laundering can be detected by correlating cryptocurrency wallet addresses with illicit activities. Law enforcement officials can also set up traps to capture criminals engaged in illegal transactions. Some portions of the deep web allow users to overcome legal restrictions to access content that is not lawfully available in their geographical location.
Latest News
Because the deep web is not fully-indexed with mainstream search engines, often the only way to find such sites is to know the exact internet address to use. There are some specialized websites or search engines that catalog some deep websites. For instance, academic resources on the deep web may be found using platforms like PubMed, LexisNexis, Web of Science, or Project MUSE. The Deep Web constitutes a multifaceted realm on the Internet that evades detection and accessibility through conventional channels such as popular search engines or major web browsers. Its content remains beyond reach due to either partial indexing by search engines or the imposition of password protection measures. While the deep and dark web offer undeniable benefits, users must navigate them responsibly.
Why Visibility Into The Deep Web Matters More Than Ever
(The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you.
- The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web).
- Also, you can set a strong password to protect your message and choose how long it will take to expire.
- These methods include using CAPTCHAs, multiple IP addresses for the same content, non-HTML content or data that spiders cannot pick up, password protection, and unlinked content.
- Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them.
- As previously mentioned, more than 90% of the traffic on the internet is already on the deep web, so the keys to accessing it safely are virtually the same as the keys to accessing the open web safely.
Do I Need A VPN For The Deep Web?
For comprehensive protection against scammers, viruses, and ransomware across every layer of the internet, get Norton 360 Deluxe. Although the deep web’s information isn’t indexed by regular search engines, it can often still be accessed. The terms deep web and dark web are sometimes used interchangeably, but they are not the same. The dark web is a segment of the larger deep web and similarly refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google.
Any online activity can carry breadcrumbs to your identity if someone digs far enough. Malicious software — i.e. malware — is fully alive all across the dark web. It is often offered in some portals to give threat actors the tools for cyberattacks. However, it also lingers all across the dark web to infect unsuspecting users just like it does on the rest of the web. Search engines generally create an index of data by finding information that’s stored on Web sites and other online resources. Enhanced Privacy and AnonymityOne of the most compelling benefits of the Deep Web is the heightened level of privacy and anonymity it offers to users.
In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.
Popular Deep Web Sites And Their Purposes
Interestingly, at the cusp of the new millennium by the US Naval Research Laboratory originally developed the Tor project. An early version of the Tor browser was created to combat the challenges presented by the lack of privacy during the initial days of the internet. Its main goal was to prevent spy communications from being discovered; however, the framework was eventually repurposed and made public. Other options exist, but they are generally created to fulfill specific purposes, such as file sharing. If the surface web is the visible part of an iceberg above water, the deep web is the part submerged beneath – much larger but hidden from plain view.
All our articles went through a multi-level editorial process to provide you with the best possible quality and truly helpful information. In fact, the deep web accounts for over 96% of all content that exists online. The only reason these sites are on the onion network is because then you can use the sites without being afraid of the consequences as whatever you share or do over there can’t be traced back to you. Another legal use of the Deep web are sites like ProPublica, which are anonymous whistle blowing sites which anyone can use to share exposing documents or truths about powerful people or agencies.
There are several programs that hackers frequently use on the dark web. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.

Unlike traditional search engines, dark web search engines are limited, sometimes unreliable, and are subject to change often. Much of the content is intentionally hidden and accessible only through direct links or known dark web websites. This makes searching for specific content much more challenging, unless you know exactly where to look. The deep web is an umbrella term for parts of the internet not fully accessible using standard search engines such as Google, Bing and Yahoo. The contents of the deep web range from pages that were not indexed by search engines, paywalled sites, private databases and the dark web. As when visiting ordinary websites, stay alert to security risks on onion sites.



