This aligns with the general ethos of privacy on the Tor network. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship. Since many users reuse passwords, attackers use stolen credentials from previous data breaches to gain unauthorized access. Users who link their Instagram accounts to third-party apps risk exposure when these services suffer security breaches. Instagram has become a prime target for cybercriminals, with stolen account credentials frequently appearing for sale on the dark web.
Your Guide To Accessing Onion Sites Securely
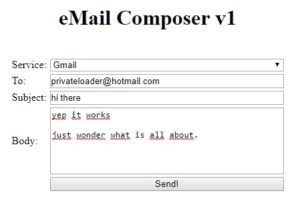
There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. Services like Random Chat connects you with random people using the same service. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble.

Can You Be Traced On Tor?
All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
Brauche Ich Ein VPN, Wenn Ich Bereits Tor Nutze?
- Tor encrypts and routes internet traffic through multiple relays, masking the user’s IP address and online activity from trackers and surveillance.
- Think about what matters most for your browsing and security, and make informed choices to navigate the dark web safely.
- Your data is encrypted in the Tor browser before reaching the ZeroBin servers.
- It is a relatively new provider but offers better features than most established VPNs.
- However, in the event of a dispute don’t expect service with a smile.
However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime.
Many need to cross international borders, and customs officials are cracking down on suspicious packages. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. Great life advice, but it’s even more valuable where the darknet is concerned. Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise. You may very well end up in the middle of a stakeout that could turn ugly.

Types Of Dark Web Sites (and What Really Goes On There)
A network browser gives you access to sites with the ‘.onion’ registry operator. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
Wie Unterscheidet Sich Das Darknet Vom Deep Web?
Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it.
Essential Tools For Safe Browsing
You could be monitored closely even if you are not doing anything illegal. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The system is designed to provide enhanced security and privacy features.

Peut-on Accéder Au Dark Web Avec Un VPN ?
Dark.fail has become one of the most trusted alternatives to the traditional Hidden Wiki. This directory focuses on providing users with verified, frequently updated links to a broad range of dark web services, including marketplaces, forums, and whistleblower platforms. Its community-driven verification system helps minimize the risk of scams and outdated URLs. Dark.fail also emphasizes user security by offering warnings about phishing sites and scam links. Unlike the Hidden Wiki, which can sometimes be cluttered with unverified content, Dark.fail is streamlined and prioritizes accuracy and trustworthiness.
The Hidden Wiki is one of the most well-known directories on the dark web, serving as a gateway for users looking to explore .onion sites securely and anonymously. For many, it’s the first stop when venturing into the depths of the dark web. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search.

Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. The good news is that the platform will not see what you copy/paste. Your data is encrypted in the Tor browser before reaching the ZeroBin servers.

This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity.
This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. mark it means it has been verified as a scam service and it should be avoided. Hackers manipulate users into revealing their credentials by impersonating trusted contacts or Instagram support staff.|For instance, e-commerce websites have utilized Haystak to improve product search functionalities, providing a more streamlined shopping experience for users. In the academic realm, researchers have leveraged Haystak to access hard-to-find resources, enriching their studies with otherwise inaccessible information. In an age where data breaches are becoming alarmingly common, maintaining online privacy is more crucial than ever. Haystak stands out by prioritizing user privacy, ensuring that your searches remain anonymous and your data secure. It acts as a sentinel, guarding your digital footprint as you navigate through potentially treacherous waters.|Stay safe and informed as you explore the deeper layers of the internet. With Tor Browser, you are free to access sites your home network may have blocked. Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. Managing files effectively is fundamental to secure, reliable IT operations. BitLocker is one of Microsoft’s most powerful security features, offering full-disk encryption to …}
This includes password-protected sites, private databases, academic journals, and, notably, dark web services accessible only through networks like Tor or I2P. The Hidden Wiki is a gateway to these deep web resources, offering links to .onion sites that cannot be found via Google or other surface web search engines. Thus, users who want to explore hidden, uncensored, or private content often rely on tools like the Hidden Wiki because it provides structured access to resources beyond Google’s reach. One of the primary reasons users prefer the Hidden Wiki and similar dark web directories over Google is privacy. Google’s business model depends heavily on tracking user behavior, collecting vast amounts of personal data to tailor ads and search results.