Maintained by anonymous volunteers, Torlinks prioritizes secure, modern .onion addresses and updates its database monthly to weed out dead links. While it lacks keyword search, its clean design and focus on trusted sites make it a reliable starting point for beginners and pros. The lack of filtering means I’m always on guard, cross-checking links with Torlinks or r/onions.
Even completing a transaction is no guarantee that the goods will arrive. Many need to cross international borders, and customs officials are cracking down on suspicious packages. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. Dark web forums are online communities where individuals participate in discussions on a wide range of subjects, from technology and privacy to more illicit matters. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails.
Separate Your Real Life From Your Online Persona
The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. Simply download the file, install the software, and you’re ready to use its web-based interface.
Haystak: The Premium Powerhouse For Deep Dives
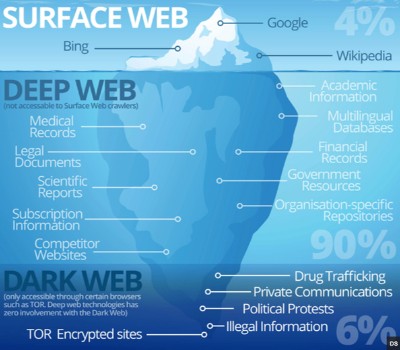
In addition, the content on the pages don’t need any special or custom configuration to access. Typically, any reference to the visible web will be to common websites with a familiar internet domain extension. Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search.
Why Choose Forest VPN?
Install Norton VPN to encrypt your internet connection and help protect the personal data you send and receive online. However, engaging with illegal content or using dark web sites for unlawful purposes is a criminal offense. The result is an entirely separate ecosystem of data that’s invisible to the clear web. That’s why many search engines have been developed specifically for this space. In addition, many dark web websites are configured to block or mislead regular crawlers. And since these sites require access through Tor, they can’t be reached over a normal connection.
Popular Dark Web Search Engines: An Overview Of Ahmia, DuckDuckGo onion, Torch, And Not Evil
If you’re curious about how to explore .onion sites safely and effectively, this guide will walk you step-by-step through the process. Let’s start by demystifying how dark web search engines actually work. Whether on the clearnet or the dark web, using search engines and other browsing tools can lead to data leaks that expose your search history and other personal information. That’s why it’s important to use online security tools that protect your personal data. Using a dark web search engine is not illegal, and accessing dark web sites and services is generally legal. However, engaging in illicit activities on the dark web is illegal—just as it would be anywhere else—and punishable by law.
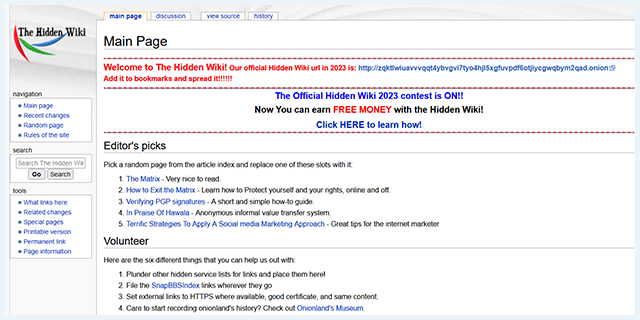
The Hidden Wiki: Best Dark Web Directory
The Not Evil is relatively safe, as it doesn’t track users; however, it doesn’t filter malicious content, so caution is still needed. Although reported as active, there is limited information on Not Evil’s current status, so availability may vary. The surface web—which we use for searching day-to-day information—is only its tip.
Use them with PGP encryption for secure communications and Tails OS to isolate sessions, ensuring sources remain protected in high-stakes environments. OnionLand indexes both V2 and V3 .onion sites, as well as I2P content, offering versatility across dark web networks. However, its reliance on JavaScript for full functionality raises privacy concerns, as enabling it can expose users to tracking or deanonymization. In 2025, I used Haystak to find a historical .onion archive of a defunct hacking forum for a cybersecurity report. The premium archive feature delivered, but I spent 30 minutes vetting links to avoid malware. Think of it as the dark web’s yellow pages, curated by anonymous volunteers who add, update, or remove links.
Practical Guidelines To Manage Risks:
- The dark web exists to provide users with anonymity and privacy on the internet.
- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
- Always prioritize security, verify .onion links, and bookmark them in an encrypted file.
- If you’re not using Tor, a VPN, or proper anonymity tools, there is a risk of being tracked.
- In 2024, I used Torlinks to find a Tor-based email service for a privacy guide.
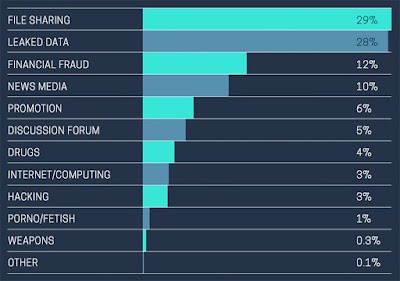
These search engines are systems that list onion links from the deep web, the main task of each search engine is to allow the display of hidden pages. Kilos is often used to discover and access dark web marketplaces, where you can find illegal drug trading. While some search engines avoid the more shady side of the dark web, Kilos embraces it, by refraining from filtering search outcomes.
While the dark web offers unparalleled privacy and freedom, it’s not without risks. From scams to illegal content, users must remain vigilant and informed. By leveraging tools like Forest VPN and adhering to best practices, you can explore this hidden world with confidence and security. Dark web search engines operate by indexing websites that have the .onion extension, which are not accessible through standard web browsers. They use specific algorithms to deliver relevant pages while ensuring user privacy and anonymity. In the end, the dark web is not just a den of iniquity but also a sanctuary for privacy and free speech advocates.
- Cracking down on many illegal marketplaces on the dark web is the result of such monitoring.
- They provide a crucial service by organizing the chaotic and often dangerous landscape of hidden websites.
- Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor.
- The dark web will continue evolving, impacting how we perceive privacy and freedom online.
- As dark web websites are not moderated, they can host a wide range of malware, such as ransomware, keylogger, and remote access Trojan.
It has a freemium model with ads, and a paid version for ad-free browsing and extra features. With the right precautions and tools, you can access the dark web more safely. Use the Tor browser, avoid unfamiliar sites, and be cautious with downloads. However, some significant security risks still remain because the dark web is not regulated. It filters content heavily and can be accessed both through the surface web (the traditional part of the internet) and the Tor browser. Although they all serve a similar purpose, these search engines differ significantly in terms of usability, safety features, and how they index content.
Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. Every communication is encrypted, so even the simplest transaction requires a PGP key. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others.
Avoid clicking unverified links from results, and cross-check with directories to prevent phishing. This setup ensures anonymity while leveraging NotEvil’s privacy-centric, no-log design. By 2030, ethical debates over content moderation could split the ecosystem, with some engines (e.g., Torch) remaining unfiltered and others (e.g., NotEvil) adopting stricter policies.
The Hidden Wiki is often likened to the dark web’s answer to Wikipedia. It’s technically not a dark web search engine but is still a useful tool to navigate the dark web and find sites more easily based on categories. Use categorized directories or reputable search engines to reduce the chance of clicking on spam or malicious links.
Going from library to library to find an item is massively time-consuming, so trust that WorldCat can do the work for you. Books, DVDs, CDs, articles, and more are all available as search engine topics. For the most part, it exists within the realm of the Deep Web, which general-purpose web crawlers do not reach. To learn about the Invisible Web and how Deep Web search engines can help, we first need to discuss the three different layers of the web in brief. When using these resources, it is crucial to follow best practices for online security and maintain vigilance. Regularly update software, use strong and unique passwords, and be cautious when sharing sensitive information or engaging in conversations with unknown individuals.



