
In some countries, exploring new political ideologies can be considered an imprisonable offense, and those who visit restricted websites could be placed on a watchlist or targeted for jail sentences. China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions. If Tor isn’t enough for you or you simply want to explore other options, I2P (Invisible Internet Project) is another powerful tool focused on privacy.

Browse The Web More Safely
The Tor project still offers no official Tor apps for iPhone or iPad, but some third-party apps are available in Apple’s App Store. While it is not always possible to discover directly a specific web server’s content so that it may be indexed, a site potentially can be accessed indirectly (due to computer vulnerabilities). PCMag is obsessed with culture and tech, offering smart, spirited coverage of the products and innovations that shape our connected lives and the digital trends that keep us talking.
- If you are in a position to report the incident safely, you should report it to the authorities immediately.
- PIA doesn’t pull punches, so it strikes back against its competition with a proven-in-court no-logs policy, split tunneling, and even port forwarding to diversify its apps.
- PCMag.com is a leading authority on technology, delivering lab-based, independent reviews of the latest products and services.
- The entry node is the first server in the Tor chain, the relay node is the middle node and the exit node is the last server in the network.
- It’s designed as an environment to elude detection, where site owners and visitors hide their identities.
Can You Be Traced On Tor?
People mostly use it for covert communication, anonymous tips submission, and stuff like that. Services like Random Chat connects you with random people using the same service. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations.

What Is The Dark Web? How To Access It And What You’ll Find
But of course, these benefits can be easily extended to those that want to act outside of the constraints of laws in other explicitly illegal ways. The dark web refers to sites that are not indexed and only accessible via specialized web browsers. Significantly smaller than the tiny surface web, the dark web is considered a part of the deep web. Using our ocean and iceberg visual, the dark web would be the bottom tip of the submerged iceberg. Venturing further into the deep web does bring a bit more danger to the light. For some users, portions of the deep web offer the opportunity to bypass local restrictions and access TV or movie services that may not be available in their local areas.
Well, there’s a reason why it’s recommended to browse with a minimized or rescaled window – you can be tracked based on your active window’s dimensions (yeah, they really can do that). So, do yourself a favor and rescale that Tor window as much as you can before proceeding. We already went through VPNs, anonymizing web browsers, and disposable operating systems, so I won’t bother reminding you about those. Well, now it’s time to fire up Tails and do a little bit of tinkering. Note that the process can take anywhere from 5 to 30 minutes depending on your machine. This multi-layered redirection ensures your actions leave no trace, offering a high level of anonymity.
Choose A Dark Web Search Engine
Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more. If you’re lucky enough, you can find it on clearnet privacy forums. The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software.
An analogy often used to depict the digital landscape is comparing the Internet to an iceberg, where the Surface Web represents the visible tip, and the expansive Deep Web lies submerged beneath. The inherent advantage of unindexed content becomes apparent in the preservation of privacy. Users cannot access a dark web marketplace without the Tor browser. And while it’s based on the Mozilla Firefox browser, Tor is not as well maintained and has page rendering issues. User accounts on the deep web contain a lot of personal information that criminals might value — that’s why access to much of the deep web is restricted.

The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight. Although the deep web and the dark web may seem intimidating and dangerous, they’re actually surprisingly simple services to get started with and use. Crawling is the process by which search engines scour the internet for new content and websites.

Official Websites And Documentation
With all this data, your ISP could create a very accurate profile of you and link it to your IP address. This is one of the reasons why it is always good to hide your IP address. Sometimes, they even know more than you would like about private matters, such as your health or finances. As much as the Darknet contains even the “good” stuff, it’s not a place you need to stumble about blindly without proper dark web safety.
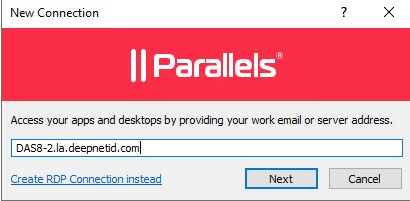
Step 3: Install And Launch Tor
In addition, it ensures that no record of communication is stored. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials.
Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Blockchain even has an HTTPS security certificate for even better protection. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user.

That effort was never fully realized, but the US military published the code under a free license in 2004. Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers. Always exercise extreme caution when using publicly posted onion URLs. If you can’t get a personal recommendation from someone you trust, verify the URL from multiple sources.
Onion links are URLs that end with .onion and can only be accessed through the Tor network. Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor.



