
It indicates a fragmentation of the cybercriminal ecosystem and diversification in attack methodologies. The report reveals that in 2024, over 100 billion stolen credential records were shared in underground forums, a 42% increase from 2023. Disregarding dark web security can lead to irreversible damage to an enterprise’s reputation, besides heavy monetary losses. The dark web may also be put to good use by whistleblowers, who can leak classified information on the dark web using websites such as Wikileaks. Special tools–the Tor Browser or the Invisible Internet Project (I2P) network–are needed to overcome these obstructions.
How To Access The Deep Web Safely
Using threat intelligence platforms to analyze the threat data gathered from the dark web also enables organizations to defend themselves against attacks more effectively. This connection methodology enables users to interact with the dark web with minimal risk of their activity being tracked or otherwise exposed. Theoretically speaking, it should be impossible to locate dark web servers and track visitors.
Deep Web Vs Dark Web: What’s The Difference?
Freenet was designed to allow peer-to-peer, anonymous communication to protect against censorship. The Onion Router (TOR) technology used by the TOR browser and the Dark Web was created by a project funded by the US Naval Research Lab (NRL). The goal of TOR was to allow secure communication by intelligence sources in dangerous environments and has since been adopted by the general public for secure, anonymous browsing. The scale and impact of the Dark Web expanded with the development of cryptocurrencies like Bitcoin, which allow semi-anonymous financial transactions to be performed on the Internet. Web pages on the Dark Web can only be accessed using the Tor browser, and users need to know the URL of the website to find it. This makes Dark Web sites a rich source of threat intelligence for organizations; however, the design of the Dark Web can make this information difficult to find.
Unlike surface websites, which are accessible and indexed by the major search engines, nothing in the deep web is ever indexed. However, to do so, you need to use a special browser that is password encrypted. Being unindexed does not necessarily imply that it is hidden; it simply means it is kept differently from the surface, indexed content.
What you can do to protect yourself is to make sure that data is not accurate anymore, not detailed enough to cause harm, and that you have multi-factor authentication enabled everywhere you can use it. Having reliable anti-malware protection active is also very important. Returning to cybersecurity issues, I need to stress that the dark web is a dangerous place, especially if you’re a non-technical person just looking to satisfy a curiosity.
Subscribe To A Dark Web Monitoring Service
This information about the implication of accessing not only the deep web but also the dark web empowers the person to make responsible decisions and fathom the complexity of internet interaction. In the end, this is advantageous because one does not risk increasing personal safety or ethical integrity in this increasingly digital world. For comprehensive protection against scammers, viruses, and ransomware across every layer of the internet, get Norton 360 Deluxe. Despite its reputation, many people use the dark web for legitimate purposes, such as secure communication for journalists, activists, and those seeking uncensored information.
There are estimated to be 1.1 billion websites on the Surface Web as of 2025 (Internet Live Stats). There’s also an increased chance of downloading malware, leaking credentials due to a phishing scam, or falling victim to financial fraud due to the lack of oversight. Accessing the Deep Web generally involves fewer risks compared to the Dark Web, but there are still some considerations.
Differences Between The Deep Web And The Dark Web

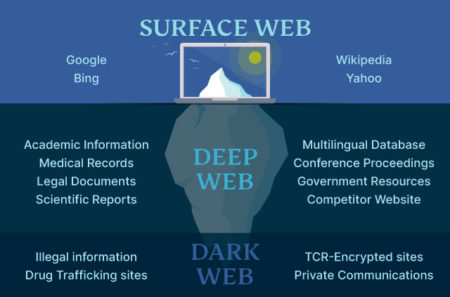
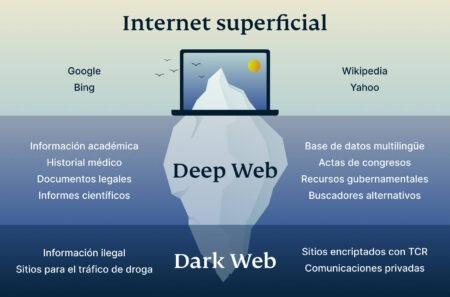
The deep and dark web are often misunderstood, but understanding each term’s meaning makes it easier to recognize their differences. These parts of the unindexed internet serve very different purposes. The deep and dark web is a treasure-trove of information on threat actor activity, however making use of this resource to protect your organization can be (to the uninitiated), challenging. The deep web is essentially the unindexed portion of the web that search engines cannot access.
Deep Web Vs Dark Web: Understanding The Differences
Similarly, logging on to the Tor browser in order to browse the dark web doesn’t mean you’re breaking any laws. The dark web’s anonymity makes it a safe space for whistleblowers, which also makes it a valuable source of information for the government. Additionally, the technology for onion routing was actually developed by the U.S.
How To Access The Deep Web
A VPN is a technology that (like Tor) provides you with a string layer of encryption to stop local networks, ISPs, and government agencies from being able to monitor your online activities. To access the purposely hidden part of the internet, you have to use special tools such as the Tor browser. Other specialist browsers like Freenet, ZeroNet, RetroShare, GNUnet, Lokinet, and Tribler are similar to Tor. However, the dark web’s anonymity makes it a breeding ground for criminal activities.
The deep web and dark web pose significant risks to individuals who access them. Both are notorious for hosting illegal activities, including the sale of stolen data, drugs, and weapons. When accessing the dark web, users are particularly susceptible to data breaches, phishing scams, and malware.
- However, the fact that in many cases the services advertised are just scams doesn’t make the dark web less dangerous or disgusting.
- Like any tool, it can be used for both legitimate and illicit purposes.
- The TOR browser provides improved privacy and anonymity on the public Internet and makes it possible to access .onion sites on the Dark Web.
- The risks of accessing the Dark Web include exposure to illegal content, potential scams, malware, and legal repercussions if one inadvertently engages in illicit activities.
- On the dark web, neither users nor web administrators reveal themselves to each other, including their identity or their location.
- When you register a domain in Trend Vision One, a scan is performed to verify whether the domain user data has been compromised by a leak—with historical data back to 2010.
August’s Top VPN Discounts
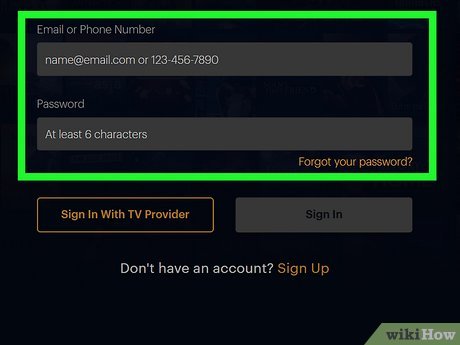
Understanding the differences between the two can help demystify the often misunderstood world of hidden online content and activities. The surface web includes websites indexed by search engines like Google or Bing. The dark web is a subset of the deep web that requires special software, like the Tor browser, to access. Known for its focus on anonymity, the dark web is often linked to illegal activities, although it also serves as a platform for privacy advocates and journalists in repressive regimes. Multi-Factor Authentication (MFA) is an extra layer of security you can enable on your accounts. MFA protects you in the event that someone gains access to your login credentials since it requires a one or more methods of authentication before they’re able to successfully log in.
It uses layered encryption (like Tor) that hides both users and servers. To access it, you need specific tools like the Tor browser, which allows you to visit sites with .onion addresses, hiding both your identity and location. The safety of accessing the deep web or dark web depends on your intent, knowledge, and the precautions you take. While both are often misunderstood, they serve different purposes and come with distinct risks. It turns out that a majority of cybercriminals, selling everything from compromised personal and financial data to drugs and hacking tools, constitute over half of Dark Web contents.
While the dark web offers anonymity and access to websites that are not inherently illegal in nature, it also hosts illicit sites for restricted materials and enables censorship-resistant browsing. As a rule, this side of the internet hides content, identities, and locations from third parties that are common throughout the ‘surface web’ (mainstream, public websites). In Tor’s case, this is facilitated by routing encrypted traffic through layers of relays around the world. But even beyond the technical complexities of the internet, the essence of the surface web can be difficult to grasp. Most definitions of the surface web reference conventional search engines’ ability to index a site.



