
Cyber attacks, identity theft, and fraud have become rampant, resulting in billions of dollars being drained from our economy every year. Law enforcement agencies have been making significant strides in taking down major dark web marketplaces in recent years. One of the biggest recent successes was the takedown of Hydra Market, considered one of the largest dark web marketplaces.
The site allows users to find and buy a vast variety of products and services. It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. Contrary to popular belief, Bitcoin and other cryptocurrencies are not the holy grail of untraceable transactions on the darknet.
All information obtained is considered inherently open and easily accessible to the public. Even though most dark web markets require registration, the process is open to the public. When registering, our usernames and other information are not linked to any individual or organisation. We also disclosed the names of these markets, because these names are well-known within the dark web community.
As a result of today’s action, all property and interests in property of the blocked person described above that are in the United States or in the possession or control of U.S. persons are blocked and must be reported to OFAC. In addition, any entities that are owned, directly or indirectly, individually or in the aggregate, 50 percent or more by one or more blocked persons are also blocked. Persons are also prohibited from causing or conspiring to cause U.S. persons to wittingly or unwittingly violate U.S. sanctions, as well as engaging in conduct that evades U.S. sanctions.
Darknet Markets Explained: Navigating The Hidden Web
When considering data collection, the crawler’s downloader will require additional time to wait for the data to be downloaded locally 20. Moreover, certain markets implement security mechanisms slightly differently on the Tor network than on I2P. For example, the Bohemia market on the I2P network does not use anti-phishing mechanisms although they do on the Tor network. Dark web markets have always been very dynamic and full of potentially unknown features or quirks. We noted that three markets (i.e. Royal Market, Tor2door Market and Vice City Market) were closed at the time of writing the first draft (December 2023) of this work.
Products And Services
The OFAC has sanctioned Bitpapa, TOEP, and Crypto Explorer for their involvement in the financial services sector of the Russian Federation’s economy. Décary-Hétu called privacy coins “essential,” and said they represent a new reality for law enforcement to adapt to. “I don’t know that I have an immediate aversion to privacy coins. I do, however, feel like there needs to be some regulation around it,” he said. Cryptocurrency analytics firm CipherTrace filed two patents in 2020 for Monero tracing technology and released “tracing virtualization” tools last summer for qualified government agencies and financial institutions. While the U.S. has not put as much pressure on exchanges, a number of major exchanges like Coinbase do not facilitate Monero exchanges. “It has been tested. There are other coins that can provide some level of privacy, but for some reason, Monero is the one that probably has the best crypto and the best means of hiding transactions,” he said.
Dangers Of Url Redirection Attacks In Today’s Digital Landscape
The researchers also found several indications of scams regarding the selling of RaaS. Most of the renowned RaaS vendors had gained their high rating from credit card or drug related sales and not because of RaaS. COVID-19 has wreaked havoc on all shipping-centric industries, drug sellers included. Criminologist Andréanne Bergeron estimates that only 21% of darknet market transactions resulted in on-time deliveries during the height of pandemic lockdowns in the spring. Hackers exploit personal data to access bank accounts, secure credit cards, and commit tax fraud. In 2025, these techniques are expected to evolve, with more sophisticated methods emerging.
The History Of Darknet Marketplaces
(b) Relative difference between the top percentile and all vendors, future success. (c) Relative difference between the top and sub-top vendor percentile, current success. (d) Relative difference between the top and sub-top vendor percentile, future success. As 2025 approaches, these insights from dark web forums reveal the pressing need for heightened cybersecurity measures. Persistent threats like account takeovers and identity theft will continue to grow, while emerging risks such as smart home exploits, disinformation services, and AI-driven social engineering pose new challenges.
At the time, it had over 600,000 users, 17,000 listings, and approximately €250 million in transactions. Authorities seized €7.8 million and arrested operators in Germany, Spain, Sweden, Romania, the Netherlands, and the US Europol leads takedown of Archetyp. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions.
- This constant cat-and-mouse game between criminals and law enforcement fuels an ongoing evolution in the darknet marketplace ecosystem.
- Protecting your account credentials is another key step in ensuring your overall security.
- Moreover, if you must use public Wi-Fi, ensure that you use a VPN to mask your browsing activity and keep yourself secure.
- As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity.
- Relying on this is what is called, universally, a bad idea, as the market could choose to retain the information and use it for blackmail, which has happened in other exit scams.
Malware Sales
Positive scores indicate that vendors achieve higher normalized network centralities or activity indicators than non-vendors on average. Virtually no one bought hand sanitizer, PPE or COVID-19 cures from these anonymous drug marketplaces, however. Stay informed and vigilant to protect your personal and organizational data against these evolving cyber threats.
Navigating Kerberos Access Solutions
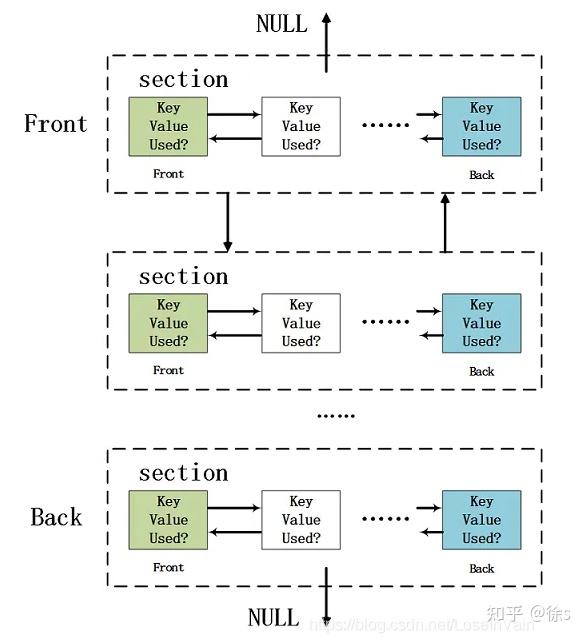
Typically, buyers will need to deposit funds into the market’s wallet first, which then will be reflected on the market’s interface. After purchasing an item, the funds will still be held in the market wallet. When the buyer confirms that the item has been delivered, the market operator will release the funds to the vendor. At this time, the funds are still (possibly) in the market address, and the vendors need to withdraw them to their private address. Escrow seems to solve the trust issue between buyers and vendors relatively well, but introduces extra security risks due to the needed trust on the market operators, which frequently exit scam. In this subsection, we explore information about financial security related to doing transactions while using the market.
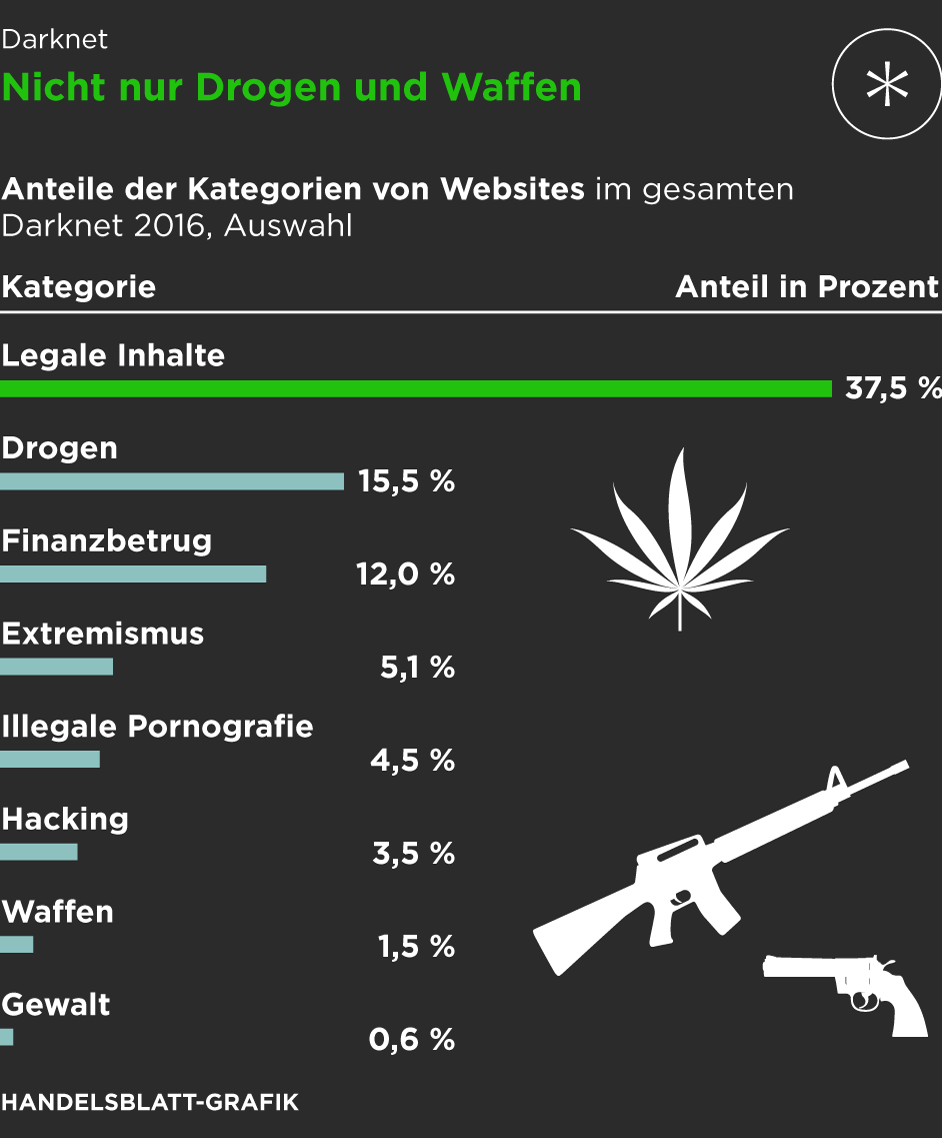
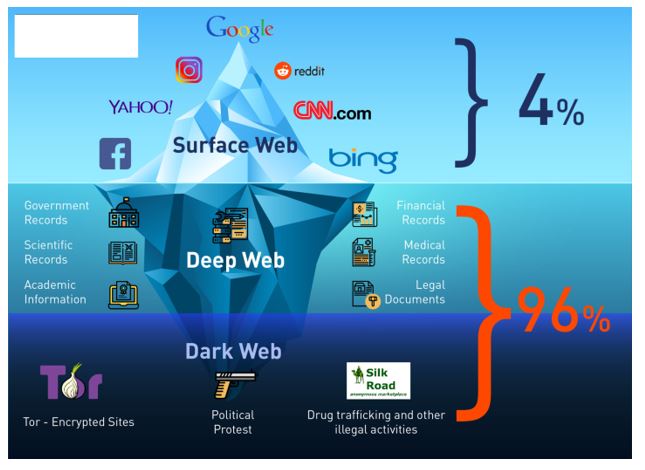
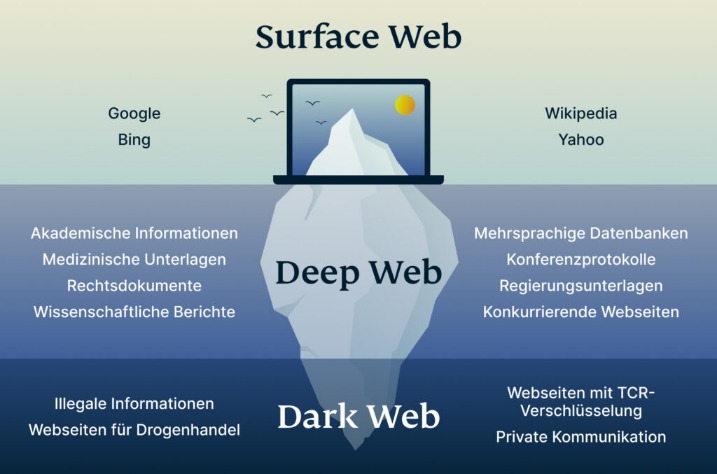
These markets operate on the dark web, a part of the internet that’s not indexed by traditional search engines and requires special software, like Tor, to access. Here, you can find anything from stolen credit card information and personal data to illicit drugs and counterfeit goods. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information. Law enforcement agencies actively monitor these markets and can track users despite anonymity measures.
One of the dark web’s most discussed threads, with more than 135,000 comments, focuses on “combo lists”, databases containing combinations of usernames, passwords, and other personal data from various breaches. Additionally, nearly 26,000 comments focus on account takeovers, where this stolen metadata is used to access accounts without authorization. “While last year’s predictions still hold relevance, we’ve noticed a significant rise in hacking courses and DIY cybercrime kits. Meanwhile, leaked personal media and customer data continue to circulate widely on these forums,” says Adrianus Warmenhoven, cybersecurity expert at NordVPN. In March, the FBI shut down Breach Forums, a criminal forum and marketplace that boasted more than 340,000 members.
Although these marketplaces are continuously shut down by law enforcement agencies, they still work today. Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones. Comprehensive validation governs each entry following the kerberos market registration guide protocols. The kerberos onion link addresses undergo extensive security verification through the kerberos market verified mirrors system. Kerberos market secure login connections preserve complete anonymity throughout all user sessions. When it comes to tackling Darknet Markets, you must remember that united we stand, divided we fall.

Therefore, while this is implemented as a functional security mechanism, its technical security remains highly unclear. In this subsection, we explore the security mechanisms applied to the account. As market operators, it is necessary to apply appropriate mechanisms to protect user accounts, which can help users avoid potential account loss, theft, scams, etc. Table 3 provides an overview of selected dark web markets’ account security mechanisms implementation.



