Blockchain analytics tools must evolve to include privacy coins and decentralized systems. Government-sponsored hacking groups actively exploit the dark web for intelligence operations, financial gain, and sabotage. These groups use dark web platforms to sell stolen secrets, acquire hacking tools, or coordinate with other criminal organizations. Cybersecurity teams must proactively monitor for leaked data and increase resilience against ransomware and phishing campaigns. Traditional firewalls and antivirus programs no longer suffice, especially when attackers operate with military-grade tools sourced from the dark web.
Common Scams On Dark Web Marketplaces
The drug trade benefits from standardized pricing and quality controls, with some vendors offering lab-test results for purity verification. One of the key advantages of darknet markets is the accessibility of niche products. Users can find specialized items that are not typically available in conventional markets.
- Moderators often request proofs of credibility, such as verified PGP signatures, to ensure participants are not infiltrators or scammers.
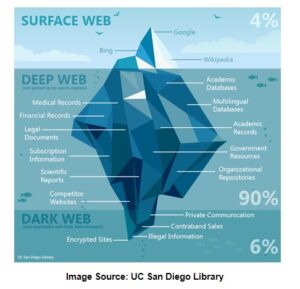
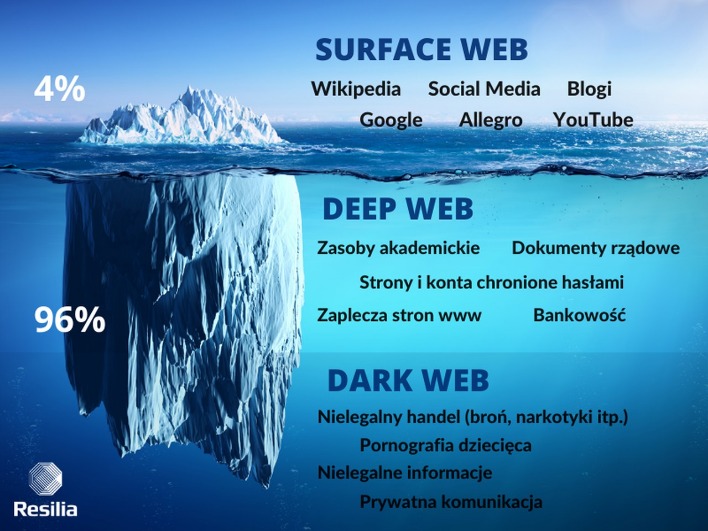
- The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025.
- They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
- The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency.
- The region has seen an increase in these threats due to the current geopolitical situation, which is likely to continue to rise if tensions do not ease.
- This way, you can catch any leaks and stop them before they cause bigger problems.
Dark Web Phishing Kits: How Hackers Sell Ready-Made Scams
Markets like Nexus and Abacus leverage decentralized infrastructure to ensure secure access via Tor or I2P. Their user-friendly interfaces simplify navigation, while escrow systems protect both parties from fraud. Vendor reputations are built through transparent review systems, allowing buyers to verify quality before purchasing.
Easy Buying Process No Hidden Fees Fast, Affordable, Trusted
Darknet markets are designed to prioritize user anonymity, which is a key factor in their popularity. Unlike traditional e-commerce platforms, darknet websites do not require extensive personal data or verification processes. This makes them an attractive option for individuals seeking discretion in their transactions.
Why Using Trusted Directories And Security Tools Is Important
We review and list tools and products without bias, regardless of potential commissions. In the face of escalating cyber threats emanating from the dark web, businesses must adopt comprehensive defensive strategies to safeguard their assets and maintain operational integrity. In 2025, the dark web presents an evolving array of threats, significantly impacting businesses and individuals alike. In adherence to the Trust Project guidelines, BeInCrypto is committed to unbiased, transparent reporting. However, readers are advised to verify facts independently and consult with a professional before making any decisions based on this content. Please note that our Terms and Conditions, Privacy Policy, and Disclaimers have been updated.
The growth of darknet drug markets reflects a broader trend in modern trade, where digital platforms are increasingly relied upon for their convenience and accessibility. The use of onion links and encrypted URLs ensures that users can access these markets without compromising their identity. This level of protection has fostered a sense of trust among users, encouraging further adoption. Even as major darknet platforms fall, TRM Labs data shows that the ecosystem remains highly adaptive. Following the 2022 shutdown of Hydra Market, TRM identified new Russian-language darknet markets emerging that by 2024 accounted for more than 97% of global darknet drug revenues. As darknet markets continue to evolve, their ability to combine privacy, security, and efficiency positions them as a viable option for modern trade.
- While it can be used for illegal activities, there are also perfectly legitimate forums, social networks, and communities.
- Darknet markets provide a level of discretion that is unmatched by conventional online platforms.
- For instance, AI-generated deepfake technology has been employed to craft highly convincing fraudulent communications, leading to substantial financial and data losses.
- Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement.
- However, you can trace its roots to the development of technologies like the Tor network or Freenet.
How To Access Verified Dark Web Sites

Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. For those prioritizing variety, EclipseMarket stands out with its extensive catalog of pharmaceuticals, recreational drugs, and rare substances.
Escrow Dominance
By 2023, figures like Killnet—a pro-Russian hacktivist group—were allegedly redirecting proceeds from darknet activity to support military operations in Ukraine. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.
Some platforms employ multi-factor authentication methods, compelling users to provide a secondary passphrase or a one-time code delivered through encrypted channels. This multichannel strategy enables Darknet operators to circumvent crackdowns and remain resilient. It also complicates the investigative efforts of cybersecurity experts and law enforcement agencies, who must track an ever-growing number of communication avenues and hidden marketplaces. As long as criminals can adapt by decentralizing their operations and adopting new technologies, efforts to shut down these platforms will remain a continual game of cat and mouse. Ransomware groups increasingly leverage Darknet forums to recruit affiliates, trade exploits, and launder stolen funds. Cryptocurrencies serve as the backbone of these operations, allowing attackers to collect ransoms without tying payments to specific financial institutions.
The rise of verified market lists has further simplified access to these platforms, ensuring users can connect to legitimate and secure marketplaces without the risk of phishing or scams. Additionally, the growing popularity of darknet forums and magazines has created a robust ecosystem where users can share reviews, discuss trends, and stay updated on new market links. When navigating darknet markets, users rely on updated market lists and verified links to avoid scams and phishing attempts.
Analysis Of Malware From The MtGox Leak Archive

Still, even with these crackdowns and better defenses, dark web markets just keep coming back. As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. Just like on the regular internet, phishing is a big problem on the dark web as well.
Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead. The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever. First things first, always use strong and different passwords for each account you open.