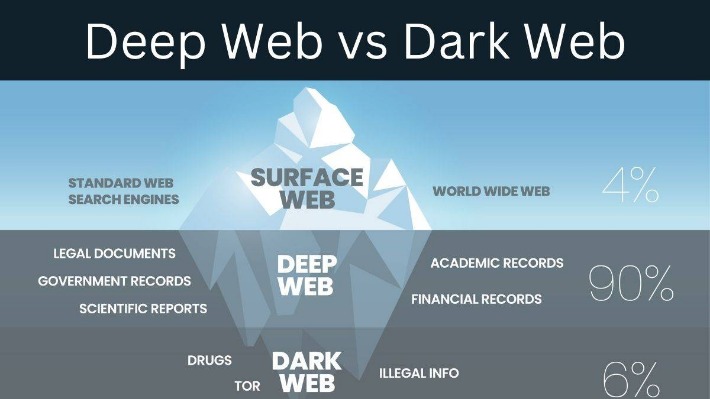
Over time, it has become an essential tool for individuals seeking to browse the internet anonymously or evade censorship in restrictive environments. The primary challenge in navigating the deep web lies in the absence of centralized search capabilities. Unlike the surface web, where search engines efficiently catalog content, deep web resources are often siloed within proprietary platforms.
Some users were drawn to this anonymity, mirroring contemporary trends in the dark web, which includes various onion sites that provide similar functionalities for illicit transactions. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more. Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Additionally, we analyse the U2U network of transactions, i.e., the transactions between pairs of market first-neighbors where the source and destination nodes are market users without the market as an intermediate.
Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. This research received no specific grant from funding agencies in the public, commercial, or not-for-profit sectors. The top three sources for Darkweb research based on the number of publications are Lecture Notes in Computer Science, ACM International Conference Proceeding Series, and the International Journal of Drug Policy. The top three sources based on the number of citations are the International Journal of Drug Policy, Forensic Science International, and Addiction. These sources are all journals and have the highest citations per publication ratio.
Telegram Shuts Down ‘Largest Illicit Online Marketplace’ After Elliptic’s Insights
Dark web marketplaces have been a significant outlet for illicit trade, serving millions of users worldwide for over a decade. First, we propose an algorithm that categorizes users either as buyers or sellers, and show that a large fraction of the trading volume is concentrated in a small group of elite market participants. We find that the dominance of markets is reflected in trading properties of buyers and sellers. Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently.
Support For Law Enforcement:
The Council of Europe Convention on Cybercrime (Budapest Convention) provides the primary framework for international cooperation against cybercrime, including those occurring on the deep web. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach. You can archive any site you want, or retrieve historical records wherever available.
How To Protect Your Identity While Browsing The Dark Web
According to this study, SDG 16 has the highest number of publications and citations related to the Darkweb, followed by SDG 3 (Good Health and Well-Being). There are strong linkages between peace and inequalities (SDG 16 and 10) and peace and good health (SDG 16 and 3), highlighting the centrality of SDG 16. We used VOSviewer 46,47 to create a visualization of the keyword co-occurrence network. Our unit of analysis was “index keywords.” We extracted a total of 5155 index keywords from the dataset, and 55 keywords met the inclusion criterion when the minimum number of keyword occurrences was set to 15.

Here, we explore some of the most sought-after items and services available on this underground exchange. Data breaches like the ones mentioned above highlight the significant threats posed by dark web black markets. Stolen data can quickly transition from legitimate systems to underground forums, where it becomes a valuable commodity for cybercriminals.

Over the past two years, the researchers have monitored roughly five posts a week and over $32,000 in transactions, all of which are made in Bitcoin. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use.
These factors collectively have contributed to the clandestine ecosystem of Deep Web Forex trading. If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using. This handy feature monitors the dark web for signs that your login details or other personal info have been leaked.
Security Blogs
We find that half of the DWM users trade through U2U pairs generating a total trading volume greater than DWMs themselves. We then show that hundreds of thousands of DWM users form stable trading pairs that are persistent over time. Users in such stable pairs turn out to be the ones with the largest trading volume on DWMs. Then, we show that new U2U pairs often form while both users are active on the same DWM, suggesting the marketplace may serve as a catalyst for new direct trading relationships. Finally, we reveal that stable U2U pairs tend to survive DWM closures and that they were not affected by COVID-19, indicating that their trading activity is resilient to external shocks.
B Using Insiders And Hackers To Get Access To Secret Information
In addition to unregulated brokers, Tor Forex also presents the risk of trading with individuals involved in illegal activities. The dark web is notorious for facilitating illegal transactions, and it is not uncommon for traders to unknowingly engage with individuals linked to money laundering or other illicit practices. This poses a considerable risk to traders’ funds and can have legal consequences. Despite its illegality, many people still turn to the dark web to engage in insider trading. The dark web is an underground world of illicit activities, and one of the more prominent activities on the dark web is insider trading. The illegal buying and selling of securities in violation of securities laws is known as insider trading, and it’s become a popular activity on the dark web.
Ready To Explore Web Data At Scale?
Investigators can learn more about the flow of money and any relationships between dark web actors by looking at blockchain data. Furthermore, insider trading is against company governance principles because it permits insiders to use their priviledged positions for private gain. Consumers thus have less faith in businesses and the regulatory bodies in charge of upholding the integrity of the market. Because it takes place in secret, it is difficult to ascertain the full scope of insider trading on the dark web.
- The site seeks to liberate information by making it free to individuals and institutions.
- Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement.
- As users reflect on this, it is crucial to acknowledge that engaging in illegal activities not only jeopardizes individual security but also contributes to a larger ecosystem of crime and unrest.
- Plus, you can access expert-backed investment research and insights and work with an advisor through Fidelity Wealth Management.
- As mentioned earlier, launching a cyberattack doesn’t require any hacking skills.
How To Access The Dark Web
Bitcoin, known for its widespread adoption in the deep web, provides a balance between accessibility and security. Monero, on the other hand, is preferred for its enhanced privacy features, making it a popular choice for those seeking maximum anonymity in their darknet trades. In summary, TorZon Market stands out in the deep web for its extensive selection of hidden products and services. Whether you’re looking for digital goods or physical items, this invisible marketplace on the Tor network provides a comprehensive and secure trading environment. As with any dark online marketplace, caution and discretion are advised when navigating through its encrypted pages. The currency of choice on TorZon is typically cryptocurrencies, which are favored for their encrypted and private nature.
Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers. The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud. Significant technological innovations and trends have reshaped dark-web marketplaces over recent years. In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns. Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data.
Why Can’t I Access Onion Sites?
Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. Still, the existence of this content is a grim reminder of the dark web’s potential for abuse when left unchecked. It’s also a marketplace for digital mercenaries; you’ll find everything from solo hackers offering their skills to well-organized groups that take on more complex or high-stakes projects. Some even have connections to criminal organizations and, in more serious cases, government-backed operations.



