It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. However, in order for its services to gain more traction, BidenCash decided to release details for more than 1.2 million cards in one go.
Dark Web Credit Cards: Understanding The Risks And Methodologies
- While you could find all sorts of products on Silk Road, drug sales quickly became prevalent because of the profits it raked in.
- The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services.
- Because the merchant requires equipment to clone the card and must send the buyer a physical product complete with PIN number, the price for cloned cards is much higher.
- It is illegal and unethical to engage in activities that exploit stolen credit card information.
- Established in 2020, Awazon Market has quickly become one of the most famous darknet marketplaces.
- Like traditional economies, the underground market comprises sellers (supply), buyers (demand), and intermediaries.
This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves. These listings often include detailed descriptions, user reviews, and even shipping guarantees. In recent years, leading dark web markets have grown more advanced.
A Criminal Underground With Certain Limits
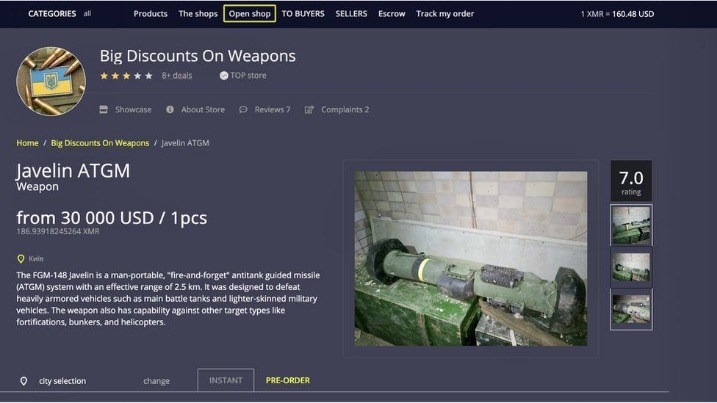
This marketplace accepts payments via Monero but also supports the Escrow system. Many of the stolen card numbers were hacked using a tactic cybersecurity experts call “brute-forcing,” the report said. In brute-forcing, a computer tries to guess your password, testing a series of numbers until it gets it right, possibly in as few as six seconds.

How Do Dark Web Markets Work?

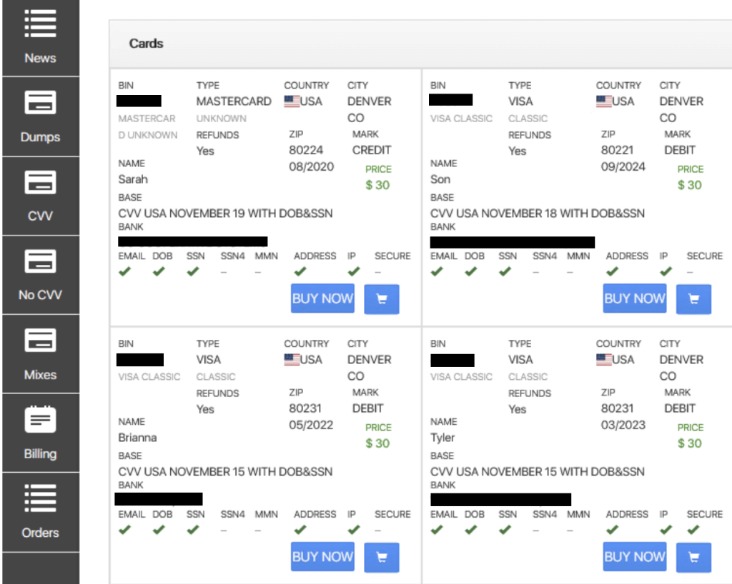
PayPal accounts sell for $2 to $10 per account, with accounts holding more money costing even more. The black market for identity data is an underground, illegal marketplace, often operating on the dark web, where stolen personal information is bought and sold. This market facilitates the trade of sensitive data, ranging from individual records to massive databases of compromised information, fueling identity theft and other cybercrimes. Buyers can include other criminals, malicious actors, and even potential nation-states. In our scenario we are going to legally transfer $1,000 USD out of a regular bank account and into a mathematical system of binary codes, and then enter a neighborhood of the Internet largely used by criminals.
Those credentials often include Social Security numbers and the date of birth. The consequences of dark web data breaches can be devastating, leading to identity theft, financial losses, reputational harm, and even national security risks. The ease with which stolen data can be traded on the dark web amplifies the impact of these breaches and makes them a significant concern for individuals and organizations worldwide. The black market for credit cards is a lucrative business, with some sellers offering cards with high credit limits for as much as $1,000. The ease of obtaining a black market credit card is concerning, with some sellers offering them for as little as $10.
Microsoft Strengthens Security After China-Linked Attacks
This section is solely for informational purposes, and it is strongly advised to refrain from engaging in any illicit activities. Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here. The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage. Like other marketplaces, it also requires registration for new users and accepts payments in Monero. Empire Market is a dark web shop that resembles the AlphaBay marketplace.
What Should I Do If My Card Is Stolen?
You can use your real information—you aren’t doing anything illegal. In about three days you will be given a fraud test and have to identify small transfers in your Dwolla and personal bank account. Once your account is confirmed, wire any amount from your personal bank to Dwolla from a lump sum or the estimated price of your purchase you have in mind. After you confirm the transfers, your legit money will now be stored in a new global bank with less restriction than US banks.
Protecting Yourself From Dark Web Credit Card Fraud
- It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero.
- In the first eight months of 2022, SOCRadar discovered that threat actors in the dark web usually posted about selling or sharing finance-related data.
- Japan, the UAE, and Europe have the most expensive identities at an average of $25.
- Apart from the dark web markets that are operating online today, some raided platforms influenced many markets.
- You can use your real information—you aren’t doing anything illegal.
- Active buyers are also eligible for free gifts and dumps depending on their volume.
To avoid falling victim to these scams, it’s essential to be cautious when entering sensitive information online. This includes using strong passwords and enabling two-factor authentication. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. The second category consists of data stores, which specialize in stolen information.
This reconnaissance can be passive, involving open-source intelligence gathering, or active, involving more direct probing of the target’s systems. Although the dark web is frequently linked to illegal activities, some trustworthy companies and organizations do use it. To send and receive messages secretly, dark web technology was developed by U.S. military researchers.

Find out precisely where attackers are targeting you and how to get there first. Join host Becky Bracken and Uptycs researchers Amit Malik and Ashwin Vamshi on Aug. 17 at 11AM EST for this LIVE discussion. One of the distinguishing features of Fresh Tools Market is its focus on providing up-to-date, freshly obtained tools and credentials. Mega Market, established in 2016, experienced a surge in popularity following the takedown of the Hydra market. Launched in 2021, Abacus Market caters primarily to English-speaking users. MuckRock is a non-profit collaborative news site that gives you the tools to keep our government transparent and accountable.

Understanding The Data Breach Cycle

This low cost makes it accessible to a wide range of individuals, including those who may not have the means to obtain a legitimate credit card. Hundreds of millions of payment card details have been stolen from online retailers, banks and payment companies before being sold on online marketplaces such as UniCC. But that’s not all; there are also cardholder details such as their full name, address, date of birth and telephone number as well as email address. Pretty much everything you would need to commit credit card fraud or launch phishing attacks against the cardholder. They also abuse promos, costing U.S. retailers $89 billion in 2021.
Participants communicate through various channels, place their orders, and get products. Black-market evolution mirrors the normal evolution of a free market, with both innovation and growth. Buyers may use the data for various purposes, including identity theft, financial fraud, account takeovers, and other malicious activities. The cycle is complete when the stolen data is used to generate profit or cause harm.



