The dark web alert system is designed to urge you to take action before any significant harm is done. These listings often include detailed descriptions, user reviews, and even shipping guarantees. Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy.
- Users face vulnerabilities like market volatility, scams involving fake escrow services, compromised wallets, or theft through phishing schemes targeting crypto transactions.
- Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
- Welcome to Black Ops Market, a darknet colossus carved from the digital abyss in May 2020.
- You’ll get stolen credit cards, remote desktop account info, personal details, and various logs.
- It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
- Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
We And Our Partners Process Data To Provide:
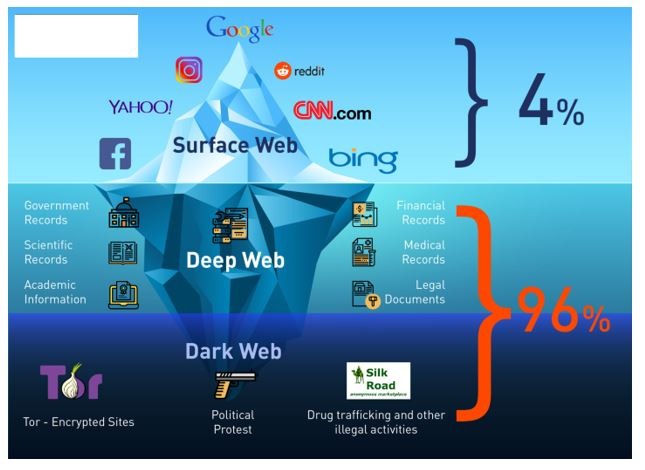
Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. As the darknet continues to grow, its markets are expected to adopt even more sophisticated tools for secure trading, further enhancing the user experience and solidifying their role in modern commerce. This market specialized in selling marijuana related products and magic mushrooms, with no “hard drugs” for sale.
Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa.
Top Dark Web Marketplaces Of 2025: A Deeper Dive Into Illicit Trade Markets
Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof. Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity. Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity and expose users’ real-world identities. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions.

To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed. In due course, the framework was remodeled and made public as a secure browser.
Identifying Malicious Onion URLs

Not every visitor is a criminal, but this is where most cybercrimes begin. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction.
- Monero’s privacy features include ring signatures that obscure transaction origins, stealth addresses that hide recipient identities, and RingCT technology that conceals transaction amounts.
- The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
- The more proactive you are, the better you can protect yourself against identity theft and other cyber threats.
- Taking the necessary precautions makes tracing your activities on the dark web difficult.
- Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware.
What Are Dark Markets?
Functionally, accessing DNMs and using them requires quite a few extra steps to protect the anonymity of the buyers, sellers, and server admins. To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser. TOR Browser is a free, modified version of the Firefox web browser configured to connect to the TOR network. Let’s get this straight — not everything on the dark web is illegal or harmful. In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored.

Which Darknet Markets Accept Zcash
Just as there are new entrants, the dark web has its veteran markets too, and Brian’s Club is one such market. It has been in operation for more than a decade since its debut in 2014. Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity.

Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship. Using a dark web search engine is a great step towards enjoying a more secure experience while shopping on the platform. Not all marketplaces you want to visit can be accessed through regular search engines. In addition, mainstream search engines also track your searches and collect personal information.
Cryptocurrency Transactions

Every potential participant’s credentials must be vigorously vetted before they can join. That way, they aim to create secure forums and limit outsiders like law enforcement. Likewise, law enforcement agencies each day continue to fine-tune their strategies to get past these networks. For instance, a factory employee can secretly slip away with one and sell it on the darknet markets.
Its intuitive interface and advanced search features make it easy to find local and global products. The marketplace extensively vets vendors listed within its deep web environment that offer a wide range of product portfolios, including security solutions, digital services, and specialized equipment. It stands as a reliable alternative to the defunct Alphabay Market as it continues to position itself as the premier source for advanced privacy-focused digital commerce. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar.
Quick Links
In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization. Standard search engines index these websites and are accessible without special configuration. Our standard escrow period provides ample time for product delivery and buyer verification. This timeframe accommodates international shipping and allows buyers sufficient time to inspect and confirm their orders before funds are released to vendors. This additional security measure ensures only the account holder can access and manage funds, providing ultimate protection for your cryptocurrency assets.
This makes it extremely difficult to find out who you are transacting with. Wasabi is one of the most popular cryptocurrency wallets on the dark web. ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. It allows you to search for images, maps, files, videos, social media posts, and more. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge.
Bitcoin remains the primary currency for transactions, providing a seamless and secure payment method. The integration of multi-signature wallets and escrow services further minimizes risks, ensuring that both buyers and sellers are protected throughout the transaction process. These features have significantly reduced instances of fraud, making darknet markets a reliable option for drug trade. Prior to its takedown by law enforcement, narcotics traffickers and cybercriminals openly traded in illegal drugs and services on Nemesis, which was designed with built-in money laundering features.



