
Cybercrime services are more commonly sold through marketplaces, but you can usually find someone offering hacked servers, computer logins, and stolen data on such forums. Encrypted communication channels on the dark web allow users to message back and forth in an anonymous online environment. However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely.
Can Cybersecurity Teams Use The Dark Web To Track Threats?
When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails. The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it. Advocacy groups are also reaping the advantages of the darknet because, here, the term of censorship is as popular as HTTPS.
Is It Legal To Access The Dark Web?
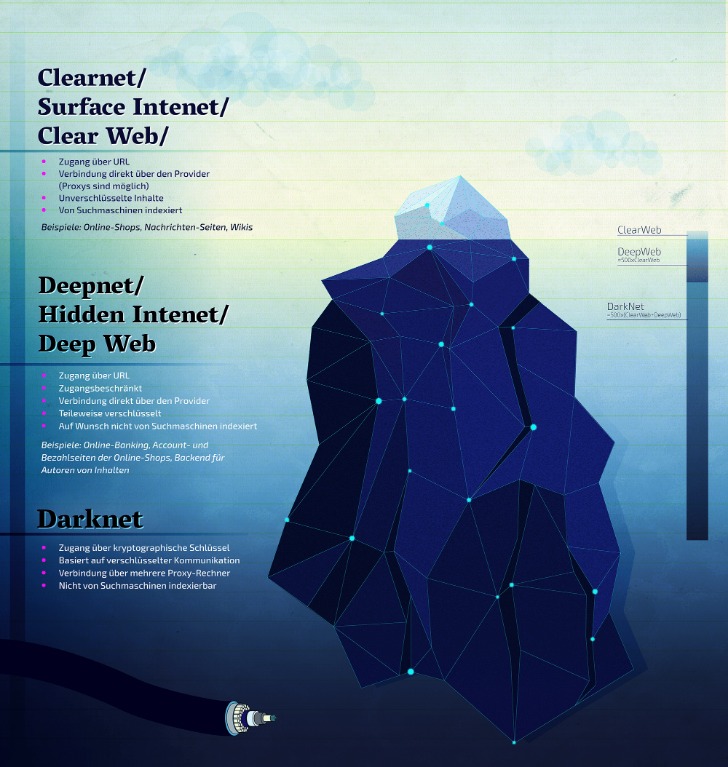
Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. It includes media and archives which cannot be crawled and indexed with current search engine technology. The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. Actually, the basic purpose of the Tor is anonymity and anonymity is not illegal in any single country.
MGM GRAND Market
It is also used to facilitate human trafficking, money laundering, and worse. The dark web (often referred to as the “darknet,” “black web” or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them.

FAQs About Darknet Markets On Reddit
The Tor software (and its dedicated Tor Browser) is probably the most famous of these, though there are others, including I2P and Freenet. It’s hard to estimate just how big the deep web is, but the commonly cited research (albeit from 2001) puts the deep web at 400 to 550 times the size of the “surface web.” And with the rise of bitcoin, the “currency of choice” on the dark web, virtually anonymous payments are easier than ever. Radar Rundown The dark web consists of many websites with uncensored information; choose a suitable … In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. In fact, your data might be up for sale on the dark web already.
- With this setup, your ISP sees Tor usage, and your VPN provider sees the final traffic after it leaves Tor.
- The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites.
- However, some Tor users do so to facilitate illegal online acts.
- In attempting to access the Dark Web, there’s an invisible line that a person acknowledges they’re crossing – or maybe they don’t.
- Each closure reverberates through the darknet community, often leading to the emergence of new platforms—only to face the same fate as their predecessors.
- There’s no guarantee that placing an order with any DNM vendor will be safe or shipped.
Why Secure Access Matters
These relays are run by volunteers around the world who donate their server bandwidth. If the surface web is the tip of the iceberg and the deep web is what’s below the water, then the dark web is what you’ll find deep in the blackest waters below. The darknet refers to the peer-to-peer network itself, whereas the dark web is the content that is served up on these networks. When you log in to internet banking, you’ve navigated to a specific location online, but one that’s not served up in Google results.

Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations. The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose. Websites and data on the dark web do typically require a special tool to access. To counter takedowns, developers are turning to decentralized DNS systems like Handshake and InterPlanetary File System (IPFS).
Do I Have To Use A VPN?
People mostly use it for covert communication, anonymous tips submission, and stuff like that. Always remember that the dark web is a people-centric community. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. Services like Random Chat connects you with random people using the same service.
The surface web is the portion of the Internet that traditional search engines such as Google, Bing and DuckDuckGo can crawl and index. Pages here follow standard Web protocols, allow automated “spiders” to read their content and are designed for public consumption. When you type a query into a search bar and click a result—say, reading this very article or checking today’s weather forecast—you are on the surface web. Because its sites are openly linked, the surface web represents only a small fraction of total online content, but it feels vast because it is the most visible.
Reports and discussions about red rooms are mostly rooted in myth and sensationalism fueled by the anonymity of the internet. In short, red rooms appear to be more of a modern-day urban legend than a verified reality, blending horror fiction with the fears of the digital age. To the mods specifically, no sourcing whatsoever happens, i only provide a setup guide and pointers on where to go from there, i never send any links, recommend vendors or need anything in return.
- It offers a unique feature where your device traffic is first sent through the VPN and rerouted through the Tor network.
- Hidden Facebook is hardly the only social media client on the dark web.
- The significance here lies in the potential damage to individuals and businesses.
- The Tor Browser is a modified version of the Mozilla Firefox browser and includes the TorButton, TorLauncher, NoScript, and HTTPS Everywhere Firefox extensions, along with the Tor proxy.
- Additional marketplaces like AlphaBay and Hansa flourished and fell, hybridizing with escrow services, online reviews, and encrypted communication to create a more intricate system.
Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. For example, the deep web is often a platform used by political activists who own a blog. But it also contains other news and religious sites, private discussion forums, and medical records. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search.
This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe. One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web. This ensures that your real IP address is hidden from the first Tor relay (it sees the IP address that your VPN provider supplies).

How To Get On The Dark Web Safely FAQs
Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users. Obviously not all Tor users, but you never know whether someone might be looking into you. It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity.
The MITRE ATT&CK framework provides a comprehensive view of adversary tactics. Explore the Darknet securely with this brief guide using the Tor Browser. As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with.
Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever. First things first, always use strong and different passwords for each account you open. Even after Silk Road went down, dark web marketplaces haven’t slowed down.



