
Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You should also consider freezing your credit to prevent identity theft. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers.
The Hidden Wiki
Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search. These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions.

Escrow Services
- The only difference is that it passes your traffic through random nodes before reaching the destination.
- In summary, the Tor Browser is your gateway to the darknet, providing a secure and anonymous way to explore and access resources that are otherwise hidden from the standard internet user.
- Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures.
- Discover everything about what a darknet market is, top marketplaces, security threats on them, and learn how to protect your data online.
- The legality depends on your activities and your country’s specific laws regarding darknet use.
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info.
Anonymity Through Tor
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa.
Search Darknet
Designed for the elite darknet operator seeking streamlined access, surgical control and unmatched discretion. The seller does not make clear how they are obtaining these cards, but threat actors are known to clone cards, or access banking information from stole credentials, particularly through Stealer Logs. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
Ketamelon Expose: How NCB & Binance Brought Down India’s Top Darknet Drug Syndicate
Desnake Market features an intuitive interface, enhanced security measures, and a diverse range of products, from digital goods to various illicit items. The market was designed to foster a trustworthy environment with robust vendor verification processes and user feedback systems. Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing.
How Much Is Stolen Data Sold For On Darknet Markets?
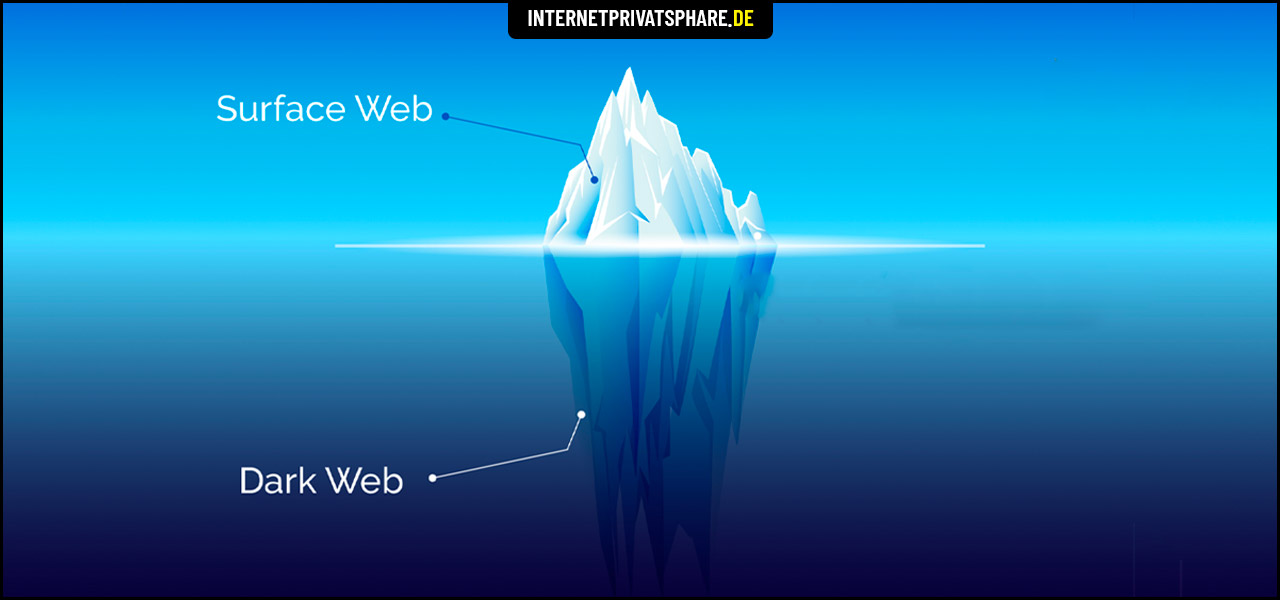
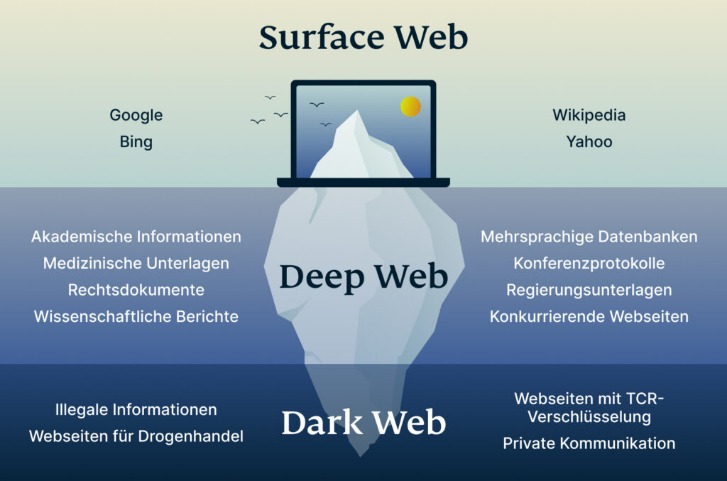
Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.
Abacus Market: Overview And Key Features
Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
The Ares onion address provides access to a decentralized marketplace that prioritizes security without compromising functionality. With regular updates and a dedicated development team, Ares continues to set the standard for darknet commerce in 2023. One of the key features distinguishing Ares market is that we use Moner, a privacy-oriented cryptocurrency, as our primary means of payment. Moner allowed our Ares customers to make purchases using complete anonymity, providing an additional level of protection from external participants in the Ares darknet link market. Ares also has several mirrors that work separately from each other, and if some Ares onionmarket mirror does not work, you can try switching to another one.
How To Find New, Active Dark Web Links

They even have a Telegram channel to provide their clients with live updates. Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace. Just as there are new entrants, the dark web has its veteran markets too, and Brian’s Club is one such market. It has been in operation for more than a decade since its debut in 2014. Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity.
It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals.
The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down.


