The device reads the data and steals the information from the credit cards swiped at the source....
wpadmin
Five Greek teenagers were brought before the main court of Rhodes last week to answer for allegedly...
Most likely, the native account on your device has full admin permissions by default. Many malware take...
Look online or contact your carrier to find out what you need to do to enable them....
A piece of tape over your webcam essentially prevents any possible remote activation by malware. Assume that...
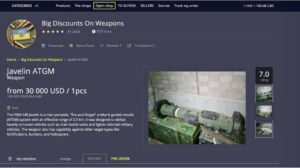
It includes media and archives which cannot be crawled and indexed with current search engine technology. To...
Always ensure you’re on the real version, like the one you’re reading now. This site is updated...
Developed under the aegis of the non-profit Tor project, with sponsorship from the U.S. government and various...
This is a tricky topic, as privacy and traceability when selling and buying Bitcoin depend so much...
The second category consists of data stores, which specialize in stolen information. In 2023, the dark web...