We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc. Although other coins are used, such as Monero recently, Bitcoin is still the mostly used in the ecosystem, being supported by more than 93% of markets7,9. The pre-processing relies on established state-of-the-art heuristics to cluster addresses into entities, such as cospending, intelligence-base, and behavioral clustering39,40,41,42. The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction.

How Do We Calculate Our Crypto Valuations?
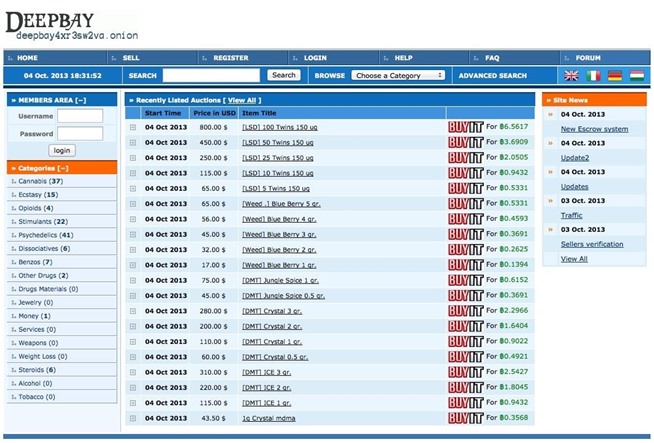
Now that you understand what the dark web is all about, you might wonder why other people do things on it. Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not. For each entity, we keep track of the cumulative values of the six features for each transaction performed by the entity over time. To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows.
While hiring a hacker might sound like something out of a movie, it’s a very real threat. Businesses may use these services to sabotage their competitors, while individuals may seek revenge or simply want access to private information about someone. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there. Now, that is not to say illegal behavior is completely beyond detection. The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable.

Common Scams And Fraudulent Activities On Darknet Markets
The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser.
It has a bidding feature, with new batches of stolen data being frequently added. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. Never log in with your real name or reuse passwords from other accounts.
When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users.
The Silk Road
By contrast, trading volume on DWMs was negatively affected by COVID-19, mainly due to shipping delays37,38. The reasons for the differential impact of COVID-19 on U2U trading vs. DWM trading are difficult to pin down. One hypothesis is that U2U pairs managed to find better shipping logistics; another hypothesis is that they were seen as a safer way to trade than DWMs at a time of crisis. The starting point for this paper is the identification of U2U networks around DWMs. We analyse 40 DWMs for the time period spanning from June 18, 2011 to January 31, 2021.
Why Is It Critical To Monitor Dark Web Marketplaces?
The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. These geopolitical dynamics intensify the complexity of cybercrime, creating multi-layered threats that affect both public and private sectors globally.
Abacus’s Rise To The Top Of The Western DNM Ecosystem
These charts and their information are free to visitors of our website. The most experienced and professional traders often choose to use the best crypto API on the market. Our API enables millions of calls to track current prices and to also investigate historic prices and is used by some of the largest crypto exchanges and financial institutions in the world. CoinMarketCap also provides data about the most successful traders for you to monitor.
Exit Scams
If a seller encourages you to opt for other well-known and commonly used payment methods, then the person is likely to be a scammer, and you must not make any deal with them. Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware. Thus, use the best antivirus software that protects against these online threats. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year.
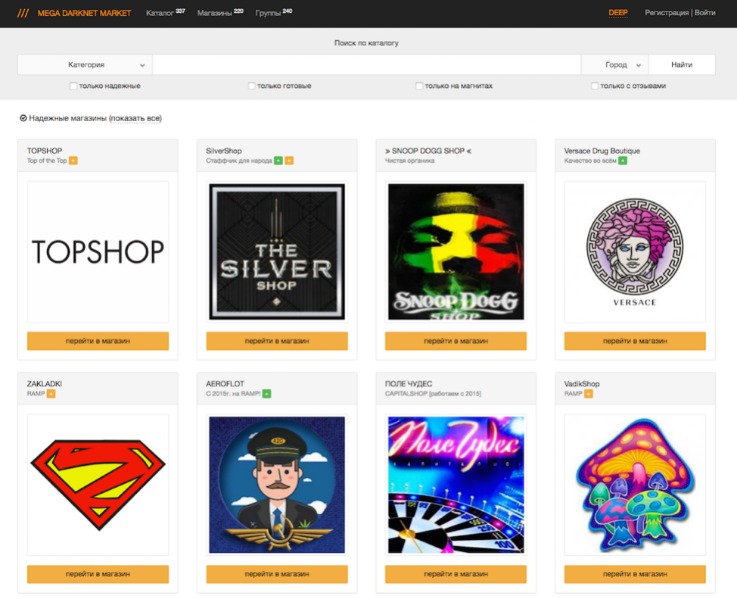
Full Network
By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. Following Europol’s takedown of Archetyp Market (one of the most established darknet platforms) on the 16th of June, users migrated to Abacus, making it the largest Bitcoin-enabled darknet market in the West by volume. Understanding both the lawful and unlawful scenarios helps provide a balanced view of their practical applications in 2025. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions. Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations.
- The marketplace is much more organized, which makes it easy to use and navigate.
- However, they all share the same moniker — every coin issued after Bitcoin is considered to be an altcoin.
- Reporter David Morris breaks down the Tornado Cash trial, Roman Storm’s conviction on money transmission charges, and…
- These hidden digital spaces host a variety of illegal and illicit activities, from drug trafficking and weapons sales to data breaches and financial fraud.
- Join millions, easily discover and understand cryptocurrencies, price charts, top crypto exchanges & wallets in one place.
Set Up Tor Browser
Monero’s ring signatures, stealth addresses, and RingCT obfuscate transaction details—enhancing privacy and hindering traceability The Rise of Monero. Sites such as Abacus and Russian Market accept both currencies to broaden their appeal. Exclusive Monero usage signals a heightened prioritisation of anonymity. The stablecoin issuers are fighting back, with the Tron-led T3 Financial Crime Unit, a group comprising of Tron, USDT-issuer Tether and TRM Labs freezing over $100 million in illict funds. OKX removed XMR and other privacy-focused tokens including dash DASH$23.43 and ZCash (ZCH) at the end of 2023.
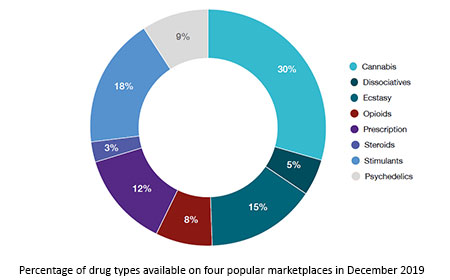
The Dark Web Privacy Dilemma: Linguistic Diversity, Talkativeness, And User Engagement On The Cryptomarket Forums
Decentralized autonomous organizations (DAOs) even govern some of these markets. Such models ensure that the market remains community-controlled and resilient to outside interference. Monero is also popular among cryptojackers who hack into computers and steal other peoples’ power supplies to mine their own cryptocurrencies. Note that just because a site or service is running on an encrypted, hidden network does not necessarily mean that it is illegal or dubious. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. When transacting, make sure it’s peer-to-peer and not through an exchange or other intermediary.
While law enforcement typically continues to target the largest darknet marketplaces like Archetyp, it has moved away from multi-DNM takedowns such as 2014’s Operation Onymous. Instead, law enforcement agencies now appear to focus more closely on the vendors. Without vendors, darknet marketplaces cannot operate or generate profits, making them a more strategic enforcement target. Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services.



