Before digging deep into how to buy cc from the dark web, it’s important to note that stealing a credit card is a serious crime, and one should not involve themselves in any such activity. Law enforcement constantly checks the dark web, and anyone guilty must bear the repercussions. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams.
Knowledge-sharing In The Carding Community
You could receive an email or a message from what might look like a legitimate company, such as an online retailer or bank, but it is a fraudster. In the message, you will be asked to click on a link and enter your credit card details, which the scammer will then capture. The shop offers stolen card data from around the world for as low as $0.15 per item and uses verification and automated checks to check the validity of the cards people put up for sale on the platform. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims.
How Much Is Your Personal Information Sold For On The Dark Web?
Modern loyalty solutions integrated mobile payments, rewards and ecommerce technology to get customers to keep coming back. Mador recommends that merchants carry out penetration testing, via a third-party security company, to scan websites and applications on an ongoing basis. “We report when we see security issues—missing patches, nonsupported software, or using out-of-date versions of programs,” and then recommend steps for remediation. Of all the data breaches analyzed by Trustwave in the company’s “2019 Global Security Report,” breaches originating from magnetic stripe data comprised 22 percent of compromises in 2017, but only 11 percent in 2018.
How To Unblock Bajaj Finserv EMI Card Online

Learn to fetch data, analyze content, and generate reports automatically. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data. Russian Market is considered to be one of the most popular, reliable, and valuable marketplaces. Unlike the name implies, Russian Market operates in English and doesn’t necessarily have a link to Russia or Russian speakers. These details are needed for physical use such as withdrawing money from ATMs.
- Additionally, securing transactions with a 3-D Secure ACS (Access Control Server) solution plays a pivotal role in bolstering the overall fraud prevention strategy.
- Customers who lose their card data to fraud may turn to a different card while waiting for a replacement card, threatening the top-card effect of passing all spending across one preferred card.
- Instead of card numbers and CVVs, criminals steal usernames and passwords that they’ve gathered either through phishing or malware.
- In the relentless battle against cyber threats, financial institutions must deploy proactive strategies and technologies to mitigate risks and protect customers, especially in the context of compromised credit card feeds.
- These black markets allow buyers and sellers to make anonymous transactions using a combination of encrypted messages, aliases, and cryptocurrency.
How To Protect Yourself From Dark Web Credit Cards Scam?
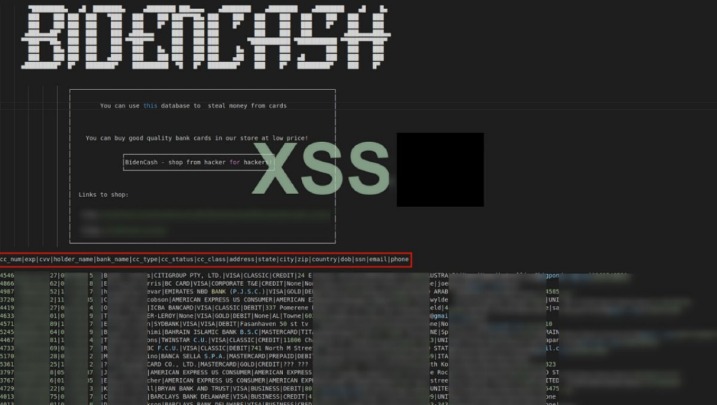
Stolen credit card details are often sold on platforms and websites dedicated to, and branded as, carding websites. There’s an underground ecosystem where sensitive data is bought, sold, and traded—not just on the dark web, as you might expect, but also on publicly accessible websites, channels, and forums. Among these are platforms dedicated to carding—a cyber crime niche centered on the large-scale use and abuse of stolen credit card information. Additionally, consider using virtual credit cards or prepaid cards for online purchases, as they limit exposure to your personal credit card details.
Recommended Content
“We do not operate with exact numbers of payment card details sold on the dark web, as NordVPN has only analyzed a set of statistical data provided by independent researchers,” the release said. Consumers also need to follow key best practices to reduce their risk. Financial data can leak in many ways—through phishing attacks, data breaches at online services, or poor account security.
Regularly Updating Security Measures

As data breaches become more common, and scammers grow more sophisticated, this is a reality many people are having to contend with. While SSN, name, and DOB are all fairly standard in fullz, other information can be included or excluded and thereby change the price. Fullz that come with a driver’s license number, bank account statement, or utility bill will be worth more than those without, for example. Social Security numbers and other national ID numbers are for sale on the dark web but aren’t particularly useful to cybercriminals on their own. The threat actor behind the AllWorld Cards marketplace has a clear goal in mind.
Card Data And Markets
Research by BitDefender has revealed the common prices for a range of illicit goods, from credit cards to credentials databases and more. Once you find a forum or market that offers the service you’re looking for — such as stolen passports — signing up for them is not unlike creating an eBay account. The main difference is that purchases are made with cryptocurrencies, and quite often such sites are far more secure than their clear web counterparts. Passphrases, distributed denial-of-service (DDoS) protection pages, and multifactor authentication are all quite standard on many darknet marketplaces. Many tracker apps link directly to bank accounts for up-to-the-minute info.
So, if you are curious about the mechanics of the Dark Web and how credit card transactions take place in this hidden realm, read on to discover the secrets of this nefarious underworld. AllWorld . cards has been operating since at least June and already has more than 2.5 million stolen cards selling between at between thirty cents and $14.40 apiece, CPO says. Digital banking has transformed both consumer banking and the threats posed to banks and their customers.
More than 9,000 active vendors selling fake IDs and credit cards reported sales in the several thousands. In the relentless battle against cyber threats, financial institutions must deploy proactive strategies and technologies to mitigate risks and protect customers, especially in the context of compromised credit card feeds. Additionally, securing transactions with a 3-D Secure ACS (Access Control Server) solution plays a pivotal role in bolstering the overall fraud prevention strategy.

Some criminals organize stolen card data by ZIP code, according to Novak, “because it makes it harder to conduct fraud detection,” he says. This is because criminals can purchase cards to use in their own geographical locations to limit the chances that their transactions will be flagged. In the ever-evolving landscape of cyber threats, businesses face not only financial losses but also significant reputational damage when targeted by fraud actors on the dark web. Monitoring the deep and dark web becomes imperative for proactive defense against such threats. Lunar, our dark web monitoring tool is designed to empower individuals and businesses in this battle against cybercrime.
In the dark underbelly of the web, cybercriminals employ various sophisticated methods to exploit credit cards for illicit gains. One common technique involves acquiring stolen credit card data from online marketplaces on the dark web. These underground platforms facilitate anonymous transactions where criminals can purchase credit card information in bulk, complete with the cardholder’s name, number, and CVV. Another method employed is card skimming, where criminals install hidden devices on legitimate payment terminals or ATMs to capture card details for later use. Once obtained, these stolen credit cards are quickly sold on the dark web, where they can be used for fraudulent transactions or identity theft. Protecting your credit card information is crucial to avoid financial loss and potential legal troubles.



