Even passive activity on these sites can contribute to criminal networks. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime. Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers. This way, it becomes very difficult to trace which websites you’re visiting, and these sites won’t know where you are located. To even gain access to the dark web, all users have to download Tor. One of the biggest benefits of using Tor compared to any other browser is that no one can monitor our activities.
Tether Announces Plan To Bring USD₮ To RGB, Advancing Native Stablecoins On Bitcoin And Lightning
I was reminded that, last year, a member of the team that had led the German investigation into Wall Street Market had told me that the war on dark-Web marketplaces was unwinnable. People would continue to have illicit desires; the Internet would find a way to satisfy them. Whatever the outcome of the CyberBunker trial, the operation against Xennt has provided police with an Aladdin’s cave of information on other criminal activity. One of the German officers charged with analyzing the contents of the CyberBunker servers told me that the volume of data was unwieldy, but its content fascinating. “I do not recall any case where this huge amount of criminal-infrastructure data was gathered,” he said. In her paper, Tzanetakis said that other studies have suggested that most users of dark net markets are men in their early to mid-20s who either work or are studying at the post-secondary level.
Uncovering Identity Scams: Insights From Recent Dark Web Discoveries
Furthermore, conducting a cybersecurity gap analysis ensures that SMEs can identify weaknesses and take targeted action to mitigate risks. Before diving into dark web exploration, connecting through a reliable VPN like Forest VPN is crucial. This service not only masks your IP address but also encrypts your data, adding an extra layer of security. By using Forest VPN, you ensure that your internet service provider (ISP) and other potential eavesdroppers cannot trace your online activity back to you.
Happy Chick Software: A Complete Overview Of The All-in-One Retro Gaming Emulator
As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of. It became the blueprint for other dark web marketplaces that tried to take its place. While this may all sound sophisticated, it is a financial crime and very risky. Those who use these services can still be traced and prosecuted if caught, especially as law enforcement continues to sharpen its tracking tools. Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit. Some marketplace operators first build trust by running a legitimate platform.
Buying Bitcoin (BTC)

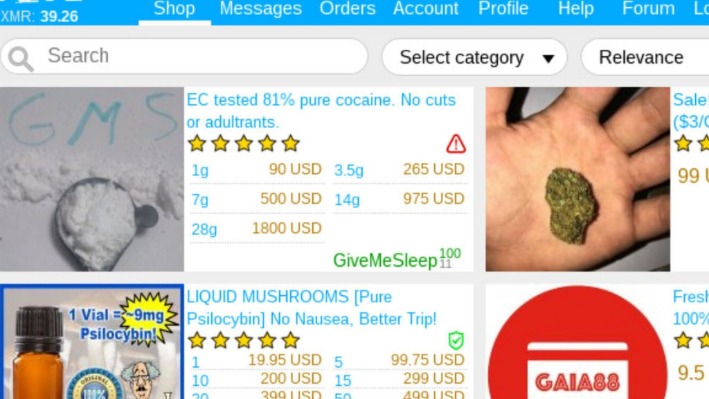
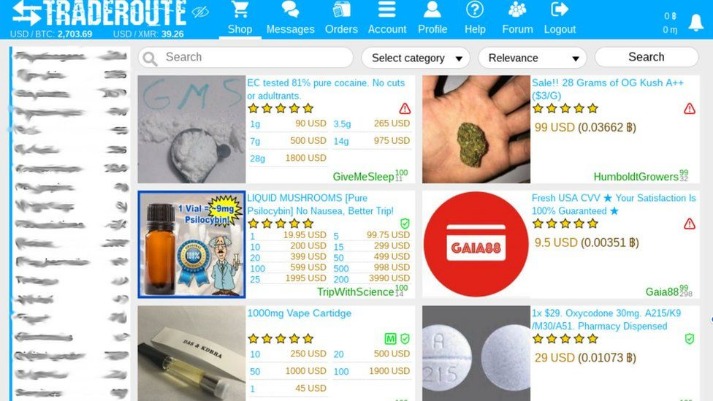
This can be done using a specialized browser like Tor, which allows you to browse anonymously. Simply download the Tor browser and connect to the network to start exploring the darknet. Deep within the hidden recesses of the dark web, a marketplace called Tor2door has emerged as one of the most intriguing and concerning platforms for security professionals. With a name that hints at its unique approach, Tor2door offers a seamless experience for buyers seeking illegal goods without ever stepping outside the comfort of their homes. As law enforcement agencies continue to grapple with the challenges posed by Torzon, its prominence as one of the best dark web marketplaces remains a cause for vigilance and monitoring.
Common Scams On Dark Web Marketplaces
With the right knowledge and tools, however, it can be a relatively straightforward process. In this guide, we will walk you through the steps necessary to buy from the darknet markets safely and securely. Encrypted communication channels on the dark web allow users to message back and forth in an anonymous online environment. However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely.
Recent Content

Use secure operating systems, encrypt your communications, and secure your devices. Utilize tools like the Tor browser, VPNs, and encrypted messaging services to maintain anonymity. Despite these takedowns, modern illegal markets have evolved by adopting decentralized hosting structures and integrating privacy-focused cryptocurrencies such as Monero to eliminate traceability. Hydra, a Russian-language Dark Web marketplace, operated for years before its 2022 takedown by German authorities, demonstrating the adaptability of these underground economies.
- He was arrested in a San Francisco library while logged in as site admin.
- By accessing reputable markets, setting up secure communication, making payments with cryptocurrencies, and ensuring a smooth delivery process, you can navigate the dark web with confidence and privacy.
- The dark web or darknet is a computer network that uses encryption and randomized relay systems to mask a user’s identity, IP address, and browsing history.
- It’s a story about how a darknet market drug dealer got started, rose to power, and how it all came crashing down.
These markets also use encryption to keep conversations between buyers and sellers private and to protect sensitive data. Altogether, these tools create a hidden online space that is designed to stay out of sight and be hard to shut down. Once hidden within the depths of the dark web, Torzon Market emerged as a formidable player in the realm of illicit trade. Security professionals express serious concerns about this marketplace due to its unique features and extensive range of illegal offerings. Known for its encrypted communication channels and user-friendly interface, Torzon has attracted a substantial community of buyers and sellers seeking anonymity in their transactions.
The dark web presents significant legal, ethical, and regulatory challenges that businesses must navigate. Non-compliance with these regulations can result in substantial financial penalties, reputational harm, and operational disruption for businesses. Even after these sites shut down, new markets keep appearing as the hidden internet is formidable to stop. Some things people do on the darknet are legal but private, like protecting their identity. Getting into darknet markets is not as simple as opening a regular website. You usually need special software like the Tor (The Onion Router) browser, which hides your location and online activity by bouncing your connection through several servers around the world.
First, in the USA, it is a federal offense to use the USPS for any of these transactions. If the buyer or seller gets caught, there are significant legal ramifications. Archetyp is a market that sells only drugs, and is still active today. The Onion Project, or TOR is the predominant anonymous computer network.
Hacking Tools And Services

Stay safe, avoid pitfalls, and make informed decisions for a secure online experience. LifeLock Standard helps safeguard your personal information, accounts, and identity. For an extra sense of security, try a powerful identity theft protection service like LifeLock Standard that offers dark web monitoring.
Remember, the Dark Web is a high-risk environment, and there are potential legal consequences for engaging in illegal activities. Therefore, it is crucial to stay within the boundaries of the law and prioritize ethical conduct. Let’s get this straight — not everything on the dark web is illegal or harmful. In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored.



