Additionally, consider using virtual credit cards or prepaid cards for online purchases, as they limit exposure to your personal credit card details. By choosing a secure payment method, you can significantly reduce the chances of your credit card information falling into the wrong hands. As B1ack’s Stash prepares to release its trove of stolen credit cards, law enforcement agencies and cybersecurity firms are working around the clock to trace the origins of these breaches and prevent further exploitation. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud.
- They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
- Features like end-to-end encryption, anonymous usernames, and message forwarding without revealing the original sender reinforced its reputation as a secure communication platform.
- By regularly monitoring your credit, using secure payment methods, and being cautious online, you can minimize the risk of your credit card falling into the wrong hands.
- You can also limit your risk by being picky about your ATMs, where criminals sometimes install card skimming devices.
Preventing Credit Card Fraud: Best Practices
Abraham Lebsack is a seasoned writer with a keen interest in finance and insurance. Carding groups and channels are easy to navigate, making them a growing threat in the dark web. A recent arrest in the Southeast Asia region marked the first time JS-sniffer operators have been caught anywhere in the world. If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API. These details are needed for physical use such as withdrawing money from ATMs.
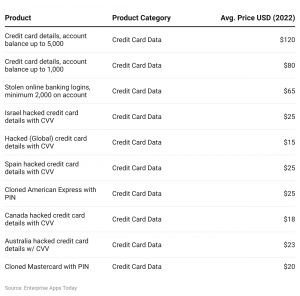
Methods Used By Criminals
In fact, credit cards are some of the cheapest such goods you can buy. Other sellers offer discounts for buying multiple cards, while the cheapest card — with between US$700 and US$1,000 on it — can cost as little as US$80. Cyber security researchers at Cyble wrote the majority of the 1.2 million cards were from U.S. users. The majority of those cards, 53% to be exact, were from American Express. Gizmodo reached out to the bank to ask whether those cards have been terminated and if any had been used for fraudulent transactions since the card numbers were released, but we did not immediately hear back. Other card issuers included the likes of Wells Fargo Bank, U.S. Bank, and Bank of America.
It features 12 subforums for different languages, with the French subforum being the most active. It serves as a recruitment and promotion hub for Ransomware-as-a-Service (RaaS) groups. Its longevity and operational security practices contribute to its popularity and secrecy. XSS, established in 2013 and rebranded in 2018, is a key forum in the Russian-speaking cyber landscape. Accessible via both TOR and the surface web, it deals with unauthorized access sales, malware exchanges, and database trading. Pompompurin launched Breached, which quickly became a hub for cybercriminals.
Ways To Protect Yourself
Companies such as my #1 pick, Identity Guard, can monitor your Social Security number (SSN) and alert you if it is being sold on the dark web or being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals. The Dark Web Hub equips law enforcement, enterprises, MSSPs, and researchers with essential knowledge to navigate dark web threats. Our continuously updated content provides in-depth insights into marketplaces, ransomware actors, and hacking forums, helping you stay informed and proactively address challenges to safeguard your organisation or community. Scanning the dark web helps you detect if your credit card number has been exposed. Once exposed, your card details can be used for unauthorized transactions or fraud.
Cybersecurity Info You Can’t Live Without
It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025. There are a variety of illegal activities that take place on telegram channels including the sharing or sale of stolen data (credit cards, banking information, stolen credentials, etc.). While this list is not comprehensive, it is a short overview of the types of activity you might see on Telegram.
Why Buy Credit Cards On The Dark Web?

Monitoring your credit is crucial in protecting yourself from credit card fraud on the dark web. By regularly checking your credit reports and statements, you can quickly identify any unauthorized charges or suspicious activity. Look out for unfamiliar transactions or sudden changes in your credit score. If you notice anything unusual, contact your credit card company immediately to report the issue.
Is My Credit Card Number Secure Once I Share It For Monitoring?
BreachForums is notable for its vast database, with over 15 billion records from 936 datasets. It features sections like Leaks and Stealer Logs and has a unique ranking system. The escrow system secures transactions, attracting high-profile threat actors. This latest breach serves as a stark reminder of the ongoing threat posed by cybercriminals and the importance of robust cybersecurity measures for you to put in place if you have not already done so. While you are thinking these are probably already old numbers no longer active, a vast majority of this enormous database originates from American victims.
Network segmentation is absolutely critical for businesses handling card data. Require multi-factor authentication for high-risk transactions, but it needs to be implemented intelligently. Financial institutions tighten their security measures to prevent fraud but that also prevents legitimate transactions as a result.
Unmasking The Underground: Navigating The Threat Of Dark Web Credit Card Marketplaces
They show recent purchases, account balances, and spending trends all in one place. Tracker apps offer a powerful way to keep tabs on credit card activity. These tools scan transactions in real-time, flagging any suspicious charges instantly. 1 This quick notice helps spot fraud fast, before major damage occurs.
- Information in the listings was entered into a spreadsheet for data analysis and statistical calculations.
- Now that we have covered the necessary steps to access the Dark Web safely, let’s move on to the process of buying credit cards on the Dark Web.
- But it’s not just the dark web that poses a problem if payment card data is stolen—it’s the entire “cybercrime underground,” says David Capezza, senior director of payment fraud disruption at Visa.
- However, the validity of the data hasn’t been confirmed yet, so it could very well be auto-generated fake entries that don’t correspond to real cards.
- This enables systems to detect fraud based on minute changes in transaction velocity, merchant category patterns, and even the time of day purchases are made.
- The threat actor behind the AllWorld Cards marketplace has a clear goal in mind.
WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
Designed for cybersecurity teams, Lunar enables advanced threat detection, credential leakage monitoring, actor profiling, and tactical intelligence extraction—at scale and in real time. Uncover the threats that are relevant to you by leveraging Lunar’s continuous monitoring of the deep and dark web. Talk to one of our cyber experts to learn how Lunar equips your team to uncover hidden threats and gain visibility into conversations that matter most. Hundreds of millions of payment card details have been stolen from online retailers, banks and payment companies before being sold on online marketplaces such as UniCC. Unlike carding shops, which primarily focus on the trade of information, carding forums serve a broader purpose within the cybercriminal community.



