By following these steps, you’ll have I2P and Hyphanet set up for secure and private browsing on the dark web. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. Whether you’re a journalist, a privacy advocate, or just curious, this guide will walk you through how to access the dark web safely and responsibly. This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor. Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country.
Standard Chartered’s Alvaro Garrido On AI Threats And What CIOs/CISOs Must Know In Their AI Journey
- You can choose 256-bit for maximum protection or 128-bit if you want a faster connection.
- It’s an overlay network that enables encrypted, anonymous connections between computers.
- IP2 is faster than Tor and offers stronger peer-to-peer security, as it uses one-way tunnels to encrypt traffic — meaning, only inbound or outbound traffic could be intercepted, not both.
- The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites.
- This vendor has access to databases that show what content is currently available on the dark web.
- If you must use one, ensure it’s a VPN with a strict, independently audited no-logs policy.
We’ve compiled a detailed guide to help you explore the Top Darknet Markets. Discover the most trusted platforms like Anubis Market, and more, complete with their unique features and security measures. Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website. When the Tor Browser is launched, you will be brought to a purple homepage with a search field for the DuckDuckGo search engine in the center of the screen.
Best Onion Sites To Discover On The Dark Web In 2024
- Upon selecting the button for your operating system, you will be prompted to download the installer, which you should save to a folder.
- The VPN’s encryption will hide from your ISP the fact that you’re using Tor.
- Yes, you definitely need a VPN if you want to access the dark web on your phone.
- There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious.
- Unfortunately, it requires you to have an invitation code to create an account.
- The dark web is shrouded in mystery, but not every onion website is dangerous.
If you must use one, ensure it’s a VPN with a strict, independently audited no-logs policy. A common inquiry from Tor users is if they should use a VPN to add an extra layer of protection. Most websites have HTTP and HTTPS versions, but connecting to the former introduces a security vulnerability. With HTTPS-only enabled, Tor automatically upgrades all HTTP requests to HTTPS to prevent this vulnerability. It encrypts data during transmission to avoid the risk of being eavesdropped.
Every communication is encrypted, so even the simplest transaction requires a PGP key. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account.
Tor-Enabled OS Alternatives To Tails For Secure Dark Web Browsing
Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual. To access a dark web address, you must use a VPN and a suitable browser (it should be Tor). The aim is to reduce your online footprint as much as possible, anonymize your traffic, and disguise your location.
Step 4: Start Browsing The Dark Web

The chances of opening websites with malicious, inappropriate, or illegal content are very high, especially if you don’t know the exact .onion website you wish to visit. The following sections will explain how to access the dark web on different devices. However, remember to be cautious when accessing this hidden part of the internet. For added protection, it’s best to use a VPN like ExpressVPN to encrypt your internet traffic and mask your IP address while establishing the initial Tor connection. Dark web sites are hidden by non-indexing, making them completely anonymous. You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content.
Download And Connect A VPN
But before we start, install Norton VPN to help protect your digital identity and stay safer online. Although browsing the dark web is not illegal, it contains unsavory activities that can expose you to danger. Remember that any website engaging in illegal activities such as drug trafficking, weapons sales, hacking, and human trafficking violates international laws and, therefore, is illegal. Anonymity on the dark web may be attractive to government critics and victims of harm who want to keep their identities private. However, criminals and malicious hackers also use the dark web to hide their illegal activities. It is designed to provide online anonymity and privacy to its users.
Using a virtual private network (VPN) is a crucial first step before diving into the dark web. While the Tor network anonymizes your browsing, it doesn’t secure your connection outside the Tor browser. A VPN encrypts your internet traffic before entering the Tor network, making tracking your online activities tougher. When people go on about the so-called dark web, they’re usually talking about onion sites, which aren’t searchable via Google or accessible via standard browsers. On the regular web, domains such as are translated into their actual IP addresses via the domain name system (DNS). That doesn’t mean it’s impossible to track users on the dark web.

How To Access The Dark Web Safely: A 2025 Beginner’s Guide
This is not what you want when also using the Tor network, as the two in conjunction will be painfully slow. The most common way to safely access the dark web is by connecting to a VPN and then opening the Tor browser. Its inherent anonymity allows everyone from dissidents to whistle-blowers the opportunity to share information free from persecution. In many cases, this information can itself be used to prevent illegal activities. Remember to uninstall any plug-ins you have before downloading, or prepare for them to be blocked – they can sometimes reveal your IP address, even if you’re using a VPN or onion router. You should also check out our article on how to find active onion sites—we’ve listed some of the best dark web directories.

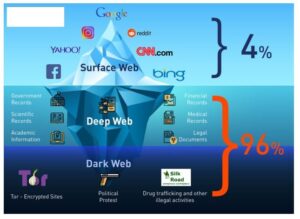
This makes it harder for websites, ISPs, or surveillance tools to see who you are or what you’re doing. Many sites on the dark web are scams, and some host illegal content. Law enforcement officials can exploit that weakness using “Tor-exit-node” monitoring techniques to expose users’ IP addresses and potentially trace activity back to the original users. If you’re on the dark web to engage in illegal activity and your traffic passes through a compromised exit node, your secrets can be exposed. The deep web is the private layer, and it’s often password-protected. The dark web has many legitimate use purposes and contains legitimate content, including dark web mirrors of popular websites and services such as BBC News and Facebook.
Let’s go through the setup process for each, as well as how to use them effectively. In this setup, the VPN connection acts as a middle layer between your device and Tor, routing your internet traffic through the VPN before it reaches the Tor network. Using a VPN (Virtual Private Network) in tandem with the Tor browser ensures an added layer of security by encrypting your traffic before it reaches the Tor network. The first step is to download and configure the Tor browser from its official website. The Tor browser is your gateway to the dark web, allowing you to access .onion sites anonymously. For example, legitimate sites, such as the BBC, the New York Times, ProPublica, and Facebook, have made their sites accessible as a Tor Onion URL to help people avoid government censorship.
Major Risks And Downsides
By observing these patterns, they can link a Tor user’s request to a server and reveal their intended destination. The last node (exit node), through which Tor routes your traffic, is delicate. In rare cases, attackers can exploit an unsecure node to monitor Tor users or gain unauthorized access to accounts. Whenever you enter any domain into the address bar, your browser uses HTTP to find and request the data from the relevant server. However, HTTP on its own isn’t secure– it doesn’t encrypt data during transmission, which leaves an opening for third parties to spy on your online activities.