Accessing the Dark Web safely in 2025 demands vigilance, preparation, and strict adherence to security best practices. By carefully following the safety procedures outlined in this guide, you minimize your risk of encountering malware, fraud, or legal troubles. Always remember, your safety online depends significantly on personal responsibility, informed decisions, and proactive application of security tips. Embrace these strategies to confidently navigate the Dark Web, preserving your privacy and security in an ever-evolving digital landscape.

Mail providers Mailbox.org and Protonmail can also be accessed via an .onion link. This may be welcome news to those in states where security services have attempted to block ‘anonymous’ email websites like these from the open web. Since Tor can be used to access websites governments try to block, the dark web can be a useful tool for people living under dictatorships to access western media.
Tips For Safe Browsing

Whether browsing anonymously or just trying to keep your regular browsing activities safe, AVP Suite has everything you need. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And though some dark web marketplaces offer user reviews, not all do. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams.
Unverified Content And Hoaxes
Then, click on New Tor circuit for this site, as illustrated below. This button will reload the site with a new circuit, which may solve the connection issue. Likewise, you’ll experience slower browsing speeds when browsing via Tor, as your requests get bounced through several servers before being processed. For example, we typed TechRadar.com into the address bar and accessed the website without any issues. To enable it, check the Always connect automatically button on the homepage.

The urban legend of ‘Red Rooms’ that features live murders has been debunked as a hoax. Some websites monitor and analyze the dark web for threat intelligence. While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims. The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity. Therefore, to ensure that you stay anonymous on the dark web, you can use Bitcoin mixers (also known as cryptocurrency tumblers) or opt for a privacy-focused coin such as Zcash and Monero.
Discovering The Dark Web: A Safe Exploration Guide

DuckDuckGo is a popular privacy-focused search engine that doesn’t track you across the web. DuckDuckGo’s dark web search engine may index pages on the dark web, but you’ll need to open it with Tor Browser. If your work or lifestyle requires you to use the dark web, however, there are ways to protect yourself. Just as you need the right tools to access the dark web, you also need the right protections to be able to stay safe on it. Tor’s anonymity has spurred many malicious actors to host dangerous sites on the network, including scams, phishing links, malware, and illegal content.
How To Safely Access The Dark Web
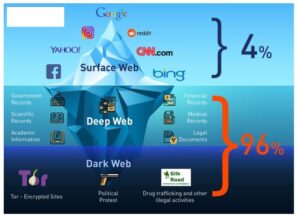
Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. Although the dark web is a small portion of the internet, experts estimate it to account for 5% of all internet content (Spiceworks, 2025)2. According to McAfee, the deep web is about 10 to 20 times larger than the surface web, making up 90 to 96% of the internet3. On iOS, the recommended option is Onion Browser, but due to Apple’s restrictions, it lacks full Tor functionality. To improve security on mobile, you should always use a smartphone VPN, disabling JavaScript, and avoiding sensitive activities on mobile.
Wide Area Network (WAN): Definition, Examples, And Technologies
When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network.
Finding Onion Sites
- Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations.
- University of Edinburgh student Ian Clarke created Freenet as a thesis project.
- Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims.
- The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people).
- Once you log in, you’re moving beyond the surface web and into the deep web.
- Several seconds of delay, compared to using a standard browser, isn’t out of the ordinary on Tor.
It is an active platform in areas such as electronic products, services and even information sharing. First of all, we will review the tools and methods you need, keeping your security at the forefront by using a secret connection. It is also important to be aware of the techniques used by hackers in this process.
While it does enable some criminal activity, it also plays a vital role in protecting privacy and free speech online. As with any technology, the impact of the dark web ultimately depends on how it is used. If you choose to access it, you should do so from a sandboxed computer with strong security controls. We hope you found this information on how the dark web works helpful. If your organization needs help with proactive security such as technical testing, advisory and compliance services, cybersecurity solutions, and training, please contact us. Whether you need virtual CISO or regulatory compliance consulting services, testing, solution integration, training or one of our many other services – our expert team has you covered.
Regularly Update Your Software

But you can do this through using open-source encryption software such as Veracrypt. Using open-source means there’s far less chance of any security flaws or deliberate backdoors as the code is constantly reviewed by the community. Whilst using Tor isn’t illegal, the encrypted data packets it uses make it fairly easy to detect. Given its relationship with crime, some ISPs and companies automatically block Tor traffic. While in theory you can buy legitimate products and services on the dark web, remember that anonymity works both ways.
It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. In this way, your browsing experience is made as anonymous as possible – if someone was ‘watching’ you, so to speak, all they’d be able to see is that you’re using Tor. For information about this, check out our guide on how to get on the dark web.
It’s hard to estimate just how big the deep web is, but the commonly cited research (albeit from 2001) puts the deep web at 400 to 550 times the size of the “surface web.” Europol says the dark web and other peer-to-peer networks are still the “main platform” for sharing child abuse material. Buying drugs, guns or the hacked personal details of millions of unsuspecting people — welcome to the dark web, where everything is off the grid. RussianMarket specializes in the sale of “logs”, CVVs, dumps and RDP access. Gannicus Oliver is an experienced tech journalist (he loves writing on emerging techs and digital privacy issues) and an online business consultant.