The website has an interface and design similar to other dark web shops. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. It’s a place people go to buy and sell illegal goods and services, from drugs to illegal weapons to tools for fraud, and worse.
Dark Web Hackers Pay For Facial Images And Supporting Identity Documents—Users Willingly Participate
Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. We will be exploring the top 10 Dark Web markets in this article. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Agents often infiltrate dark web marketplaces by posing as buyers or vendors to gather intelligence on illegal activities. Undercover agents create convincing fake profiles, interact with criminal vendors, and conduct controlled purchases. These interactions help law enforcement track the identities and operational tactics of criminal organizations.
Stay Within Legal Boundaries

Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption. Its user base is primarily English-speaking, and it appeals to more sophisticated cybercriminals. We’re back with another video in our Webz Insider video series on everything web data. At Digital One Agency, we’re here to help you build legitimate, secure, and profitable tech ventures — the kind that scale, attract real customers, and don’t end with handcuffs or disappearing acts. Darknet traders don’t want full decentralisation — they want convenient anonymity with dispute resolution. That’s hard to get without some form of centralisation, which always becomes a target.
Criteria For Choosing The Best Dark-Web Marketplaces
- Further market diversification occurred in 2015, as did further developments around escrow and decentralization.
- Accounts come with free proxies and displayed at home page with info like country, account type, balance, price, and order link.
- Fees hit 3-6%, but their beefy setup’s worth it; I saw a glitch get patched before it spread.
- Some even have connections to criminal organizations and, in more serious cases, government-backed operations.
- Takes Bitcoin or Monero, and last week I snagged a deal that shipped in three days flat.
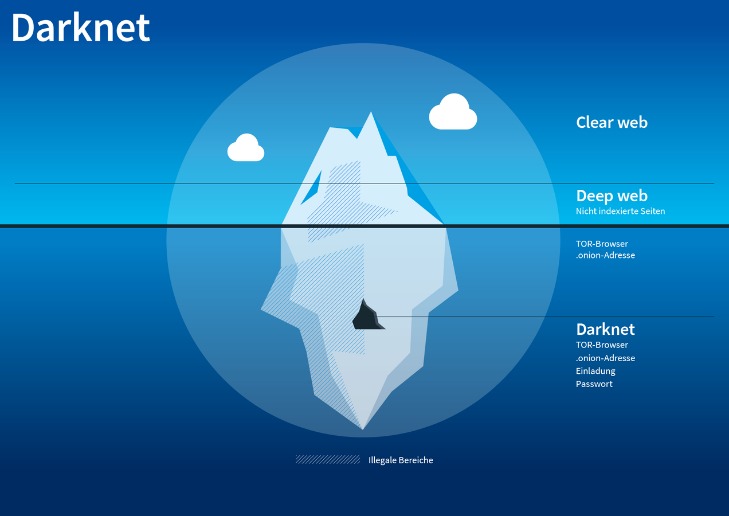
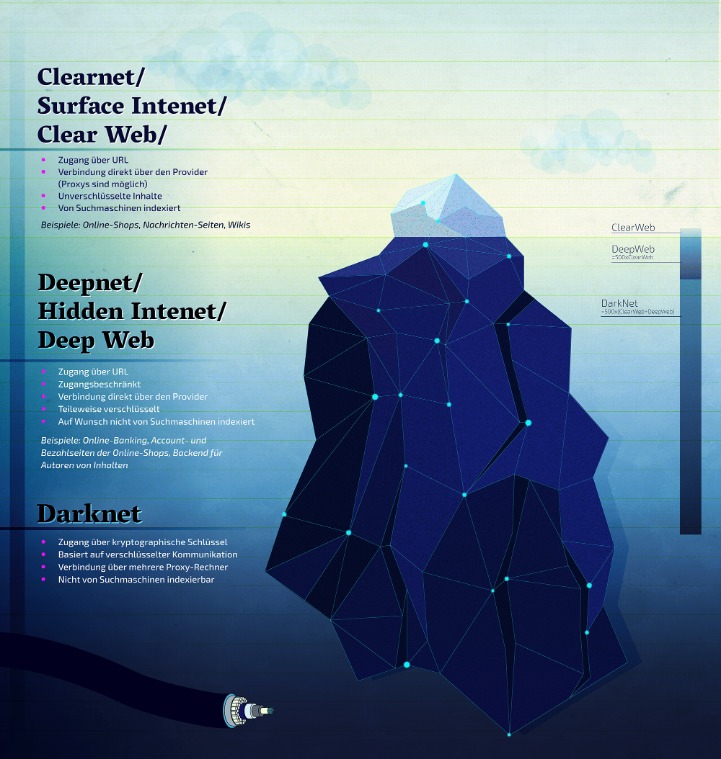
Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists of everyday private or password-protected content. The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm. Even passive activity on these sites can contribute to criminal networks. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime.
Major Risks
With frequent law enforcement takedowns, exit scams, and rising user caution, many platforms have disappeared, while others have adapted by adopting stricter security measures, multisig escrow, and enhanced vendor screening. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. All the payments were made through cryptocurrency, further enhancing marketplace anonymity.
Black And White Cloned Cards
It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity. The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots. These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.

Your privacy is our top priority, which is why we offer 100% anonymous payment options to keep your transactions secure and discreet. We accept cryptocurrencies like Bitcoin (BTC), Ethereum (ETH), Litecoin (LTC), and USDT (Tether)—all of which ensure your payment is untraceable and confidential. We believe in doing it right the first time, so you never have to worry about second-rate products or wasted money. When you choose us, you’re choosing reliability, craftsmanship, and peace of mind. Because let’s face it, when it comes to fake IDs, cutting corners is not an option.
These solutions are powered by AI technology and are put to use during the initial stage of customer onboarding. Once an identity thief attempts to log in to the victims, say, bank account or patient health portal, AI models accurately detect discrepancies in the information to detect fake or forged identities. On top of this, biometric facial recognition technologies can also be employed to enable remote identity verification through face scans. These strategies not only prevent identity fraud during the initial stages of account opening, but also allow companies to comply with mandatory KYC regulations.
Here’s What Your Data Sells For On The Dark Web

As soon as a suspicious case is identified, our specialized darknet monitoring team is informed. They analyze the facts of the case and decide on the next steps, be it direct notification of the customers concerned, further monitoring or the publication of security-critical information to protect third parties. Our continuous monitoring extends not only to forums, marketplaces and messenger channels, but also to trafficking in stolen data, exploits and access points. The insights gained from this provide our customers with strategic advantages, help them to strengthen security measures in a targeted manner and minimize potential risks at an early stage.
Sellers often use PGP (Pretty Good Privacy) encryption to secure communications and protect user identities. Additionally, escrow services act as intermediaries, temporarily holding funds until the buyer confirms the transaction, reducing fraud risks. For businesses, the cybersecurity risks posed by Dark Web marketplaces are substantial. Data breaches, leaked credentials, and intellectual property theft are common occurrences.
Law Enforcement Takedown
As we mentioned earlier, not everything sold on dark web markets is illegal. As terrible as its reputation may be, some vendors sell legitimate goods or services. Some customers even use the dark web to make anonymous purchases, especially in areas where privacy is a huge concern. So, not everyone who shops there is looking for something illegal.
The dark web is also a place for scammers to attract vulnerable and unwitting victims. The platform is also used by governmental cyber departments to identify and track potential criminals or offenders. This is made easy, because the anonymity works both ways. You can never be sure who’s really behind the other end of the line. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. The advantages of I2P are based on a much faster and more reliable network.
How Hackers Use The Dark Web To Launch Cyberattacks
At its launch, the platform accepted payments through Litecoin, but now it has incorporated support for other payment methods like Monero and Bitcoin. The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their data and communication. Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade. In addition, several fake websites impersonate the famous dark net marketplace to obtain your financial and personal information and use it for malicious purposes. Hence, you must go with a vetted-list and access them safely. The global cost of cybercrime has been on an alarming rise with the estimated loss to be in billions of dollars, with some reports indicating that the overall loss could be in trillions.
Each brought slightly more sophisticated technology, better vendor ratings, faster escrow, or new coins. These are just a few of the many facets of our lives where a criminal with access to the correct personally identifying information ad a properly designed forged document can wreak havoc. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.



