
During our tests for the research, we were able to register with a bogus email and a random username. All that one can expect from a deep web marketplace when it comes to anonymity and security. With these stolen credentials, the suspects purchased ghost gun parts and tools from a variety of legitimate websites, which they used to build ghost guns with a 3D printer, and sell for cash. A Manhattan district attorney successfully used this evidence to bring charges against one of the suspects. Deposits span from the hundreds to the tens of thousands of dollars, and the average deposit amount in 2024 was over $2,000. China-based Abacus vendors have many listings for research chemicals.
The Founder Of Silk Road, Ross Ulbricht
Total darknet market revenue fell from $2.3 billion in 2023 to $2 billion in 2024. According to Chainalysis’ 2025 Crypto Crime Report, darknet market (DNM) vendors are adapting their money laundering tactics. While centralized exchanges (CEXs) remain the dominant cash-out method, a notable shift has been toward decentralized finance (DeFi) protocols.
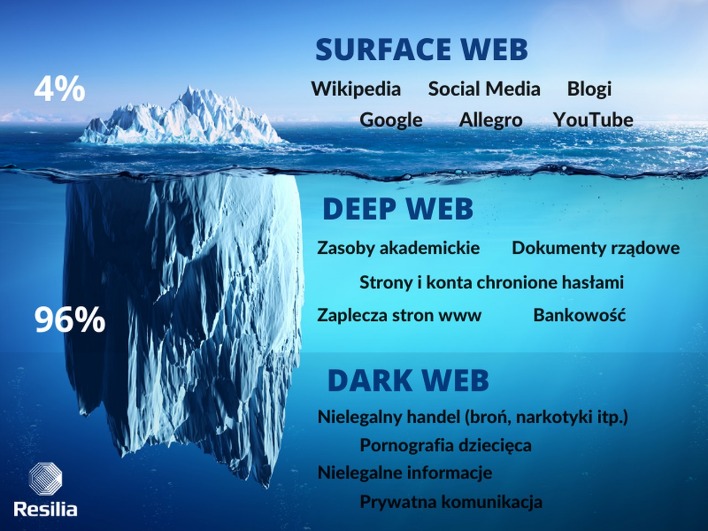
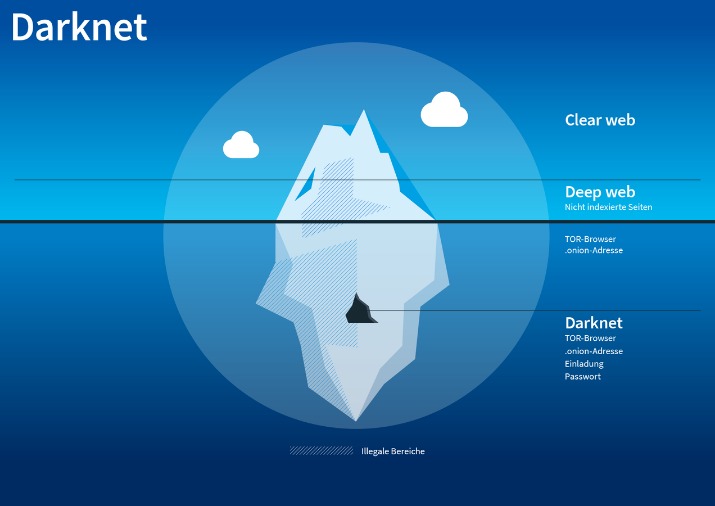
Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track.

Stolen Personal Data
The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Look for ratings below 90% or no escrow—common red flags on markets like Torrez. Download Tor Browser from torproject.org—your entry to the onion network. Some countries have just one or a few vendors with a loyal customer base and a wider selection of goods. For example, in India, one of the most frequent listings is for generic medication, which mostly comes from the first vendor shown below.
Why Is A VPN Important When Accessing The Dark Web?
They’re hinting at going decentralized in 2025—less downtime, more trust, right in line with the decentralized trend. The site’s slick, with vendor stats updating live and a checkout that’s a breeze. I’ve used it a few times, and it’s never let me down—great for folks who like their dark web with a modern twist. Telegram’s creeping into the darknet scene—not full markets, but vendor channels. I’ve stumbled on groups pushing everything from scripts to gear, often linking back to spots like Tor2door. It’s not replacing markets yet, but it’s a side hustle worth watching.
How Can I Enhance My Privacy While Accessing The Dark Web?
Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers.

Microsoft Strengthens Security After China-Linked Attacks
It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar. Cryptocurrencies and related laundering services are evolving as criminals seek to move towards more privacy-preserving currencies.

Personal Information
- If any user is found not complying with the law, strict and immediate action will be taken against them.
- You can even use a secure email provider or a burner email address whenever you visit the dark web.
- They’re tightening security and carefully screening anyone who wants to join.
- The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
- It’s free, masks your IP, and bounces your connection around so no one’s peeking over your shoulder.
The fallout for victims whose data is stolen and sold can be devastating. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives. They really don’t care about the loss and dilemma of the victims whose data has been stolen.
- Bank Secrecy Act (BSA) requires reporting on cash transactions exceeding $10,000.
- Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details.
- The site’s unique—loads fast, looks sharp, and vendors get treated right, keeping turnover low.
- Agora ran from 2013 to 2015, and it avoided the crackdown that saw the demise of Silk Road 2.0 and other dark web marketplaces.
- Transactions just below reporting requirements is one of the red flag indicators the FATF has highlighted in guidance for Virtual Asset Service Providers (VASPs) to help identify suspicious behavior.
- We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails.
Access Our Coverage Of TRON, Solana And 23 Other Blockchains
While the example above is relatively simple, more complex money laundering networks feature consolidation wallets that aggregate funds from dozens or even hundreds of intermediary wallets. Querying Chainalysis data can point investigators to major consolidation wallets, which often serve as useful leads. Conventional money launderers are onboarding to crypto using methods similar to their fiat-based strategies. Unlike crypto-native money laundering, non-crypto-native money laundering begins with the placement stage involving fiat. Typically, criminals will first use bank accounts for their fiat funds, which they then convert into crypto.
Security Blogs
Archetyp’s all about the drug game—ships worldwide, keeps fees low (1-4%). Their anti-phishing tricks saved me once when a fake link popped up; the real site’s clean layout sealed the deal. Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from … Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr… There are several other browsers you can use, such as Freenet and I2P, but Tor is the most recommended option. In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands.
We find that the dominance of markets is reflected in trading properties of buyers and sellers. Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently. Specifically, we show how the networks of multihomers and seller-to-seller interactions can shed light on the resilience of the dark market ecosystem against external shocks. Our findings suggest that understanding the behavior of key players in dark web marketplaces is critical to effectively disrupting illegal activities. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors.
To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. Moreover, sensitive personal documents are made available on the dark web. Some things, like medical records, driver’s licenses, and passport information. The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. The dark web is famous when it comes to hosting as well as spreading explicit and illegal content.



