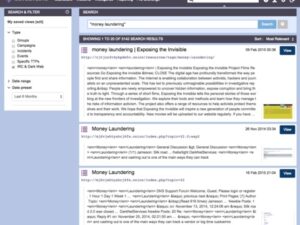
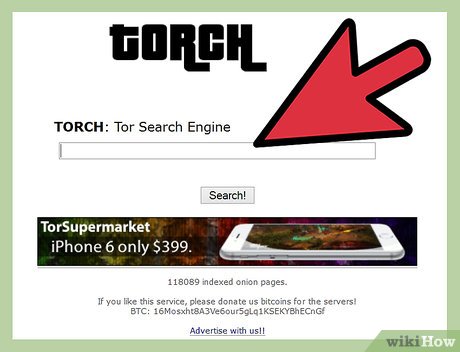
Many search engines are now offering encrypted search options, anonymous browsing capabilities, and built-in proxy services to help users protect their online identities and data. It uses advanced data mining techniques to index and analyze the deep web, providing users with valuable insights into online activities and trends. Memex is a powerful tool for investigators and researchers looking to track down illegal activities and identify potential threats. Yes, to access .onion sites including most dark web search engines, you need the Tor Browser. Some engines like Ahmia offer a surface web version, but for complete access to dark web content and for your own privacy, using the Tor Browser is essential. We’ve provided download links for various platforms in the article above.
Quick Look: Top AI Search Engines Compared Side By Side
While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor. Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls. However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way.
Subscribe To Our Newsletter
Its database is among the most comprehensive, rivaling Torch with billions of indexed pages, but it focuses on V3 .onion addresses for security. Haystak doesn’t filter harmful content, leaving users to navigate risks themselves, making it better suited for experienced researchers or journalists with robust security setups. I always cross-check its listings with Torlinks or r/onions to avoid traps, and I’ve learned to spot clones by checking link patterns. For beginners, it’s a gentle introduction to the dark web, but for pros, it’s a launchpad to pair with proper dark web search engines.

The dark web is a hidden part of the internet that requires specialized software to access. Where you can find all the resources you need to expel Google from your life. Due to the sanctions, upcoming Huawei Android smartphones couldn’t use Google, so the company decided to create their own independent search engine. Qwant initially focused almost exclusively on the domestic market in France and claimed to be the second most-used search engine in the country in 2018.
How To Stay Safe On The Dark Web
It is important to research and choose a search engine that meets your needs and security requirements. Cipher Seeker is a Deep Web search engine that specializes in uncovering encrypted and coded information. By utilizing advanced cryptography algorithms, Cipher Seeker can access hidden content on the Deep Web that is protected by strong encryption. Ghost Finder is a Deep Web search engine that focuses on uncovering hard-to-find information and resources.
New York Times
- Ahmia promotes transparency by being open-source and allowing contributions.
- Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
- Launched around 2007, The Hidden Wiki is a legendary entry point to the dark web, though not a traditional dark web search engine.
- A VPN protects your connection against everyone, not just your ISP and the authorities.
- It is an AI-powered search assistant designed to provide users with direct answers through a chat interface.
Swisscows is an example of a family-friendly uncensored search engine. It focuses on providing safe content while also respecting user privacy and offering uncensored search results. SearX is a metasearch engine that aggregates results from multiple sources, ensuring a comprehensive view of the web.
### Key Features Of Ahmia ###
In addition, its technology is open-source, and it doesn’t keep your data, which proves it is safe to use. To send a message or image via ZeroBin, you just need to copy the desired content and paste it into ZeroBin’s editor. For those needing an additional layer of security, you can set it to disappear right after viewing. This is largely due to harmful elements in the dark web, and Ahmia contains certain questionable and largely illicit links. Therefore, use NordVPN to view search results and browse anonymously.
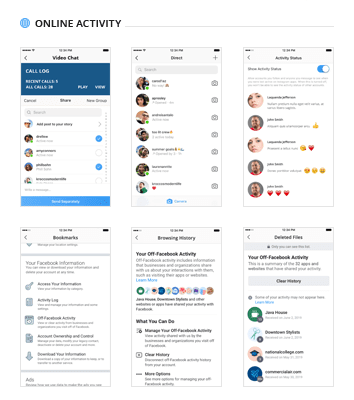
Avoid direct engagement; document evidence offline and consult ethical guidelines to prevent backlash. In 2025, use APIs (e.g., Ahmia’s) for automated OSINT, but employ sandboxing and ethical guidelines to avoid risks like malware or legal issues while analyzing trends. To safely access NotEvil, first download Tor Browser from the official site and connect via a reputable VPN like NordVPN for added IP masking. OnionLand (2022) brought surface web polish with a Google-inspired interface and I2P support, targeting mobile users and beginners. NotEvil’s Google-like interface lowered the entry barrier for beginners, while its no-log policy appealed to privacy advocates. However, its reliance on volunteer moderation and unstable .onion address limited its reliability compared to Ahmia’s rigor, positioning it as a middle ground.
What Is A Cloud Access Security Broker?
Haystak boasts an impressive index of over 1.5 billion pages from more than 260,000 websites on the dark web. It offers both free and premium services, with the premium version providing additional features and more detailed results. This sequence offers less anonymity because your real IP address is still partially exposed along the Tor path.

How To Access onion Sites Safely
While they make accessing Tor-hidden websites easier without the Tor browser, they can compromise your privacy and security by acting as intermediaries that might expose your data. Using the Tor Browser with a VPN is a safer and more secure option, as it provides end-to-end encryption and better privacy protection. It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access. However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not. To stay on the right side of the law, be cautious about what you access and ensure you follow the rules in your region. However, many are used for illegal activity and onion websites are often popular hangouts for cybercriminals and scammers.
Its .onion link is bookmarked, but I treat it as a starting point, not a destination. The dark web operates on the Tor network, a decentralized system that prioritizes anonymity over discoverability. Its .onion sites—ranging from whistleblower platforms to underground forums—are invisible to conventional search engines.
Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide. It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services. One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki.
- Data sent through the dark web is encrypted and relayed through multiple nodes hosted by a global network of volunteers.
- It blends traditional search with short summaries, giving users direct answers without tracking or targeted ads.
- With a minimalist interface, it streamlines the dark web browsing experience.
- Dark Search also delivers unfiltered results and includes a feature that allows users to directly report illegal content.
- Shenma is another leading Chinese search engine with a global market share of 0.04%.
- NotEvil emerged in the mid-2010s as a successor to TorSearch, inspired by Google’s “Don’t be evil” motto.
Designed for researchers, journalists, and privacy advocates, Ahmia prioritizes safety without sacrificing functionality. It supports V3 .onion addresses, offers an API, and maintains a modest but high-quality index of ~10,000 sites. As long as there’s a demand for the ability to privately browse the internet and, more importantly, host websites anonymously, the deep web will exist.