Since 2018, it has actively aimed to protect companies against external threats. The anonymity and lack of oversight in the Deep Web can make it a fertile ground for exploitation, including human trafficking, child exploitation, and other forms of exploitation. This can have severe consequences for vulnerable individuals who may become victims of such activities. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China.
How To Stay Anonymous While Browsing The Dark Web?
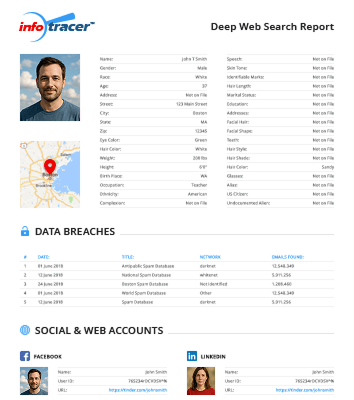
Unlike traditional search engines, Pipl looks through the Invisible Web and retrieves data from social media profiles, public records, and other online sources that are often ignored. The deep web search sites host a vast array of specialized content, including academic databases, research repositories, private company intranets, and subscription-based services. These resources may not be readily accessible on the surface web but are invaluable for researchers, professionals, and individuals with specific interests or needs. One of the advantages of using Fizzle is that it provides users with access to a wide range of academic content that may not be available on traditional search engines.
H5: Can I Access The Same Information Found On Traditional Search Engines?
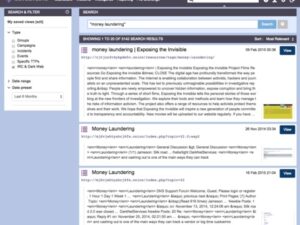
Some may log search history, contain hidden scripts, or other elements that can jeopardize user anonymity. Always choose search engines that uphold user privacy and avoid those that collect data or present intrusive scripts. Unlike the surface web, dark web search engines have no reliable mechanisms to report or take down malware-hosting websites. Clicking the wrong link from a dark web search engine can trigger malware infections, data theft, or access to ransomware.
A Quick Guide On How To Use A VPN With Tor
The 11 search engines listed here offer unique access to hidden databases, archives, and resources that go beyond traditional search methods. In an era where information is at our fingertips, the deep web often remains an enigma, shrouded in mystery and intrigue. Most of us navigate the surface web every day, blissfully unaware of the vast ocean beneath.
The dark web is full of illegal marketplaces and forums where criminal activity is advertised and discussed. Some examples include Empire Market, Dream Market and Nightmare Market. You need to know something about your topic in order to choose the next tool. To be fair, some of these sites have improved their index-ability with Google and are now technically no longer Deep Web, rather kind-of-deep-web. The continued evolution of Deepseek will likely see enhancements centered around user experience and expanding reach into newer online territories. Future updates might include improved natural language processing (NLP) capabilities, bolstering its grasp over more complex queries and multilingual support.
Other Ways To Access Dark Web Platforms
Understand what the deep web is, and how it differs from the dark web, and explore how to stay safe on the deep web. A key feature of DuckDuckGo is its strict no-log policy, ensuring user privacy. As a result, the precise number of DuckDuckGo users remains undisclosed.
For example, this is the place to start if you want to study scientific research, historical documents, or specialized databases. Accessible as a well-maintained library, it leads you to the internet’s best-kept secrets. TorSearch is a search engine designed specifically for the Tor network, which is used to access the Dark Web. It provides access to a wide variety of content, including websites, forums, and marketplaces.
Risks Of Exploring Illicit Markets
Users in countries with strict access and user laws are often prevented from accessing even public sites unless they use Tor clients and virtual private networks (VPNs). Tor (“The Onion Routing” project) network browser provides users access to visit websites with the “. This browser is a service originally developed in the latter part of the 1990s by the United States Naval Research Laboratory.
Benefits Of Using Forest VPN
These tools add layers of privacy and protect against data leaks and surveillance. Before exploring, make sure you’re familiar with the laws in your jurisdiction. Even someone’s accidental exposure to illegal content can result in them experiencing legal consequences. If you visit a site with harmful malware or Trojans, it can affect your device.
It aims to provide users of the Tor Anonymity Network with a powerful and robust search engine that helps discover different useful websites on the dark web. Moreover, Ahmia can also be used to view statistics, insights, and news about the Tor network. The dark web is a part of the internet that we can reach only with a specific tool. It hosts onion links that you can not find with regular browsers like Chrome, Firefox, Edge, or Safari. For this, the Tor browser works best as it allows you to visit dark websites while maintaining anonymity by routing your traffic through several nodes. TechXtra is one of the best deep web search engines where you can search for content that has to do with Maths, Engineering, and Computing.
BBC Tor Mirror
- However, it does not function as a regular deep search engine; instead, it provides an opportunity to access data that would otherwise be inaccessible.
- Focused on privacy and ethical legal use cases, Ahmia allows users to discover content on the Tor network without compromising their privacy.
- If your tools are incompatible, you risk exposing your identity or accessing unreliable results.
- This includes dynamically generated content, private databases, password-protected sites, and content requiring specific permissions or protocols.
- It’s important to remember that while there is valuable information to be found on the hidden deep web, there is also a significant amount of illegal or harmful content.
The concept of the deep web first gained attention in 2001 when researchers introduced the term in a study. This marked the beginning of efforts to explore the vast, unindexed parts of the internet. They often required users to manually navigate directories or rely on basic search protocols. For example, in 2005, Google introduced the Sitemap Protocol, which allowed search engines to crawl deeper into websites. This innovation made it easier to access hidden content, though it still fell short of fully unlocking the deep web.
The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events.