However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. The last item on our dark web websites list is Google Feud or rather its evil twin. For those of you unfamiliar with this, G-Feud is a clear web game where you have to guess the answers to some random or topic-related search strings. For instance, if you choose a topic (e.g. food), G-Feud will give you a string such as “can I eat…?
- SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity.
- N 2025, dark web websites frequently change domains and are often short-lived.
- It describes itself as a tool for social change and “a project to create democratic alternatives.” Riseup requires you to have the onion link as well as an invitation.
- You should also limit the number of financial transactions you make on Tor banking portals.
- As the name suggests, Dread is a hidden internet forum designed to look like the legitimate website Reddit – it’s easy to say that it’s the dark web Reddit.
Some of the reasons why it’s worth monitoring these hack forums include, ability to detect breaches early, gaining threat actor insights, and third-party risk mitigation. If you’re a company, you might want to monitor the dark web to safeguard your reputation and compliance. If you can find your data even before attackers exploit it can help you prevent PR disasters. It’s known that the best place to purchase or even exchange various hacking tools is on the dark web discussion boards. In these forums, you can get stuff like malware, hacking tools, and exploits. They’re the tools that enable cybercriminals to conduct their attacks on businesses, institutions, and individuals.
Some services are genuine; you can get what you want at an agreed fee. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code.

The New York Times — Globally Recognized News Coverage
So, before accessing the dark web, be sure you know how to do so safely and anonymously. It’s a great dark web search engine that affords users an extra layer of protection and anonymity. Some sites are perfectly legit—such as domain services and email providers. Some—like whistleblowing—may face government censorship in your country.
News And Document Archives
It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. There’s more to it than just sharing things such as hacked databases, stolen credentials, exploits, or hacking tools.

The Hidden Wiki
Pastebins are text sharing services, usually for sending and sharing text snippets. ZeroBin encrypts and decrypts text in the browser, so their servers have no way of knowing what’s happening on the browser side. One of the most straightforward ways to access to dark web safely is via Tor, so we’ve kept that in mind when compiling our list. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else.
Stay Anonymous While You Browse
- It offers a wide array of leaked data, ranging from password leaks as well as leaked databases to tools used for web development, marketing automation, SEO, and paid scripts.
- It uses TrustedServer technology on the entire server network to wipe out your data after every session.
- A VPN connection is key to gaining greater privacy, security, and freedom on and off the dark web.
- There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely.
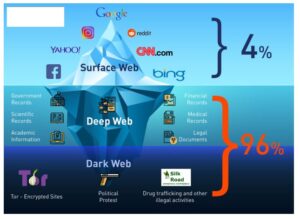
- The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
The Tor browser option for streaming comes with eleven channels with varying genres. But, honestly, if you are going on the dark just to enjoy free music, we recommend that you go for free torrent platforms on the surface web instead. If you wish to access the snapshots of these websites, just type in the domain name, and you will get the results depending on how many records exist on the website. This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. Accessing tunnels is illegal and dangerous, which is why records of these “adventures” can only be found on the dark web. If you want to access this site, do it only for fair purposes and with proper security measures.
What To Do If You See Something Illegal
This just involves turning on your VPN before you open Tor and connect to dark web sites. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together.
Systemli Onion Index

That said, you may come across advertisements while searching on Haystack. Fortunately, you can upgrade to the premium version and avoid that altogether while accessing advanced searches and results from historical onion sites. Tor’s default search engine, DuckDuckGo, does not fetch you results from .onion sites, and that’s exactly why you need a dark web search engine like Haystak.
We Helped Patch A Chromium Bug That Could Leak Your Real IP — Here’s How
Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption. Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. Your online activity and communications remain private and secret on the dark web.
New Shamos Malware On Mac: Beware Of ClickFix Attacks
To understand the dark web discussion groups needs more than looking at the data that’s leaked. It required maximum attention by looking at who leaked what, where it was posted, and in what type of context. Also, the forums tend to be recruitment grounds for a wide range of cybercriminal groups. It’s a type of collaboration that cybercriminals look for to expand their reach as well as the impact of their operations.
How Do Onion Sites Work?
A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines.