TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
New York Times
I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. While you’re at it, now might be a good time to check whether any of your personal information has been leaked on the dark web. The dark web is home to a variety of useful and legitimate resources — educational materials, encrypted email services, anonymous forums — that can’t be found elsewhere. The New York Times can also be anonymously accessed via the dark web.
How Can I Safely Access Onion Sites?
Onion sites are dark web sites that can only be reached through online routing via Tor, in which encrypted data passes through multiple nodes before reaching its destination. Decrypting the data involves peeling back layer upon layer of encryption, hence the “onion” analogy. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you.
Melhores Sites De Pesquisa Para Navegar Na Dark Web
While they might sound the same, these websites are fundamentally different. Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. The site is different from our whole list, but still worth a mention.

Collecting Threat Intelligence
However, some caution is warranted as the directory includes user-submitted links that may occasionally slip through without thorough verification. The Dark Lair aims to balance breadth of coverage with usability, making it a solid choice for newcomers and experienced users alike. OnionLinks.com is a curated darknet directory that organizes and lists active .onion sites, also known as Tor hidden services. Unlike older, spam-filled lists or unreliable forums, OnionLinks is known for its clean interface, regularly updated content, and commitment to only listing Tor v3 addresses.
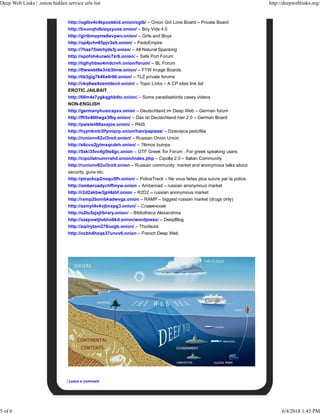
– RAMP (Russian Anonymous Marketplace)

The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing. As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. Just remember that this is a Dark Web resource, which means that much of the content is likely in breach of copyright. That said, it is one of the most famous and popular Dark Web sites, and it does have legitimate uses.
Is It Legal To Access Dark Websites?
One of the newer markets to emerge in 2021 is Kingdom Market, which has already gained recognition as a top contender. With over a year of experience under its belt, asap Market is already one of the largest and most diverse darknet markets in existence. Its extensive selection of listings categories ensures that buyers can find whatever they are looking for with ease. By following these tips and precautions, you can safely explore onion links on Reddit and navigate the dark web with confidence. You can also use Reddit’s search function to look for specific keywords like “onion links” or “dark web.” This will bring up posts and comments related to onion links that you can explore.
- Additionally, it provides community ratings and user feedback, adding an extra layer of trust.
- One of them is by using a directory of sites, like The Hidden Wiki.
- For real-time messaging, Ricochet Refresh offers decentralized, peer-to-peer encrypted chats over Tor without central servers, greatly reducing surveillance risks.
- The dark web is a subset of the deep web, where content is not indexed by standard search engines.
- We recommend using NordVPN as it offers top-notch security features, including dark web threat protection.
- Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall.
This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines. Finding data on the dark web can be challenging, in this post we’ll cover how the dark web works, how to access it, and the top 5 dark web search engines. Using a VPN like Forest VPN not only enhances your security but also contributes positively to global causes. Forest VPN prides itself on not logging user data and offers an environmentally friendly approach by reducing CO2 emissions, thanks to its battery-saving technology.
White House Market
You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
Tweak Tor Browser Settings
SecureDrop protects your privacy by encrypting your data, which makes it unreadable. Also, it doesn’t log your IP address or any information about your browser or device. Moreoever, the servers are owned by the organizations that use the service. Always use a fake name and a temporary email address when you buy something from the dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web.
Indicators Of Compromise In Threat Intelligence

Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
But online and at your finger tips, if you can make it past the surface web. RAMP, short for Russian Anonymous Marketplace, launched in July 2021 and has since earned a spot among the most exclusive and selective forums on the dark web. What sets RAMP apart is that it’s not limited to Russian—it also operates in English and Chinese, giving it broader international reach within the underground community.
It doesn’t track your browsing history, location, or any other data. It’s so secure and privacy-oriented that the Tor browser uses it as the default search engine. Some sites are perfectly legit—such as domain services and email providers. Some—like whistleblowing—may face government censorship in your country. What makes XSS particularly interesting is that it’s not limited to the dark web via TOR; it’s also accessible through the regular web, which is quite uncommon for these types of platforms. DuckDuckGo is a helpful search engine available on the Tor that allows you to browse the dark and regular web anonymously.
Like other marketplaces, ASAP Market also requires you to register for an account. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade. In addition, several fake websites impersonate the famous dark net marketplace to obtain your financial and personal information and use it for malicious purposes.